
What is Cyber Resilience? Should You Worry About It?
What is cyber resilience? is it really something that your business needs to worry about, or is it just a new buzzword?
Read More
What is cyber resilience? is it really something that your business needs to worry about, or is it just a new buzzword?
Read More
The huge data breach at Vastaamo is setting a new standard for ransomware demands as cybercriminals try a new kind of double extortion. Will it also set a new GDPR penalty record?
Read More
Cybercriminals have been working overtime, especially in Britain, serving up fake GDPR compliance notices as part of clever GDPR compliance phishing scams. Here’s how to avoid that trap.
Read More
In 2014, Apple’s introduction of the iPhone 6 was more than just an exciting iteration of its flagship product – it was the launch of Touch ID. This blockbuster device ushered in a new era of widespread biometric data use for the layman. Fingerprints had replaced passcodes as device gatekeepers, charged with protecting the most important, sensitive information.
Read More
As companies collect and store more and more personal information, they face data privacy risks on many fronts. Increasingly, they are being held accountable for protecting their customers’ digital privacy. New regulations, led by Europe’s General Data Protection Regulation (GDPR) in 2018, are quickly becoming normative in countries around the world. In total, 58% of all countries have some form of privacy regulations on the books, and another 10% are drafting legislation.
Read MoreOver a year after its widely anticipated debut on May 25th, 2018, the General Data Protection Regulation (GDPR) is still a point of confusion for many SMBs. Although our European partners have been keeping a pulse on developments for quite some time, privacy regulations are quickly pervading into the global security landscape across the US, Canada, Australia, and New Zealand with cascading consequences and implications. In order to prepare MSPs and business owners for upcoming change, the ID Agent Team will unravel how the Dark Web and GDPR are inextricably connected. But first, let’s refresh on the basics: A GDPR Crash Course Designed to protect the data security and privacy of EU citizens, the GDPR was introduced as a replacement to the Data Protection Directive of 1995. As an overview, the regulations empower consumers with greater ownership over their personal information; highlights including the “right to be forgotten”, a fortified consent process, and more stringent breach notification protocol requirements. Aside from expanding the definition of “data processing” to include collection, retention, deletion, breaches, and disclosures of personal data, the penalties associated with infractions are no laughing matter. Since its implementation, multinational corporations have seen fines amounting to $23M. Or even worse, 4% of global revenue. Dark Web + GDPR So where does the Dark Web fit into this? Just this past week, we covered a recent report by the Federation of Small Businesses (FSB) proclaiming that UK-based SMBs were suffering nearly 10,000 cyber attacks per day. Although the majority of these are serious security breaches, some are slipping through the cracks as “leaks” that go unnoticed. These manifest themselves as vulnerabilities caused by password recycling, lost devices, accidental website updates/ emails, and even rogue employee behavior. Unlike more overt incidents, data compromises are much more difficult to detect, especially for small businesses with minimal security measures in place. Therefore, sensitive information collected from such leaks ultimately finds a home on the Dark Web, without anyone being the wiser. As we know, cybercriminals will exchange valuable credentials for cryptocurrency, and then leverage leaked information to orchestrate crippling fraud tactics. In the past, companies were able to sidestep any ties back to them due to loose privacy regulations and limited feedback loops. However, those days are soon coming to an end. The GDPR mandates that companies of all shapes and sizes must disclose consumer data breaches, and will also be held liable for such accidental leaks. For example, the Information Commissioner’s Office (ICO) and National Cyber Security Centre (NCSC) of the UK has published specific guidance for risk management, data protection, detection, and minimization of impact. The Solution The global standards for data protection may be rising, but so have the solution sets for SMBs. By partnering up with MSPs who have enlisted in proactive Dark Web monitoring solutions (like Dark Web ID!), you can future-proof your company from facing GDPR fines or dealing with business process interruptions. Case dismissed. Need more proof? See what Ryan Markel, President of Take Ctrl, LLC, has to say about working with our team: “My clients are so grateful that they are not aware when their passwords are compromised that they are telling their colleagues at other companies they have to work with us”. Sources: https://www.parkersoftware.com/blog/gdpr-dark-web https://www.law.com/legaltechnews/2019/01/23/could-the-gdpr-right-to-access-make-personal-data-more-vulnerable/?slreturn=20190712111548 https://cybersecuritysummit.co.uk/wp-content/uploads/sites/29/2017/10/White-Paper-GDPR-Data-Breaches-the-Dark-Web-June-2017.pdf https://www.swknetworkservices.com/dark-web-breaches-compliance-gdpr/ https://gdpr.report/news/2017/07/03/growing-threat-dark-web/ http://www.securityeurope.info/the-eus-gdpr-and-crime-throwing-some-light-on-the-dark-net/ https://mashable.com/article/how-gdpr-changed-internet-2018/ https://lmgsecurity.com/should-your-data-breach-response-plan-include-dark-web-scanning/ https://cyansolutions.co.uk/monitor-dark-web-stop-security-breaches-fast/ Cybersecurity and GDPR: https://www.ncsc.gov.uk/information/GDPR UK’s Cyber Essentials certification: https://www.cyberessentials.ncsc.gov.uk/advice/
Read More
So you’ve been breached. Now what? Once the dust has settled use it as a learning opportunity & tune up your cybersecurity plan. We can help.
Read More
The benefits of moving your business to the Cloud have become crystal clear in recent years. It allows you to empower your aging IT infrastructure, integrate your existing tools seamlessly, scale as your organization grows and work anywhere on any device. However, as is often the case, convenience comes at a cost to security. Cloud services are no exception. In fact, the Cybersecurity and Infrastructure Security Agency (CISA) has released an Analysis Report after having conducted interviews with customers who used third-party partners to migrate their email services to O365. It found that these organizations had a mix of configurations that lowered their overall security posture and led to user and mailbox compromises and vulnerabilities. Here is what you need to know about the risks involved in transitioning to O365 and other cloud services. Default settings = Defeated settings CISA found that multi-factor authentication for administrator accounts was not enabled by default by either the customer or third-party integrator. Azure Active Directory (AD) Global Administrators in an O365 environment have the highest level of administrator privileges at the tenant level. This is equivalent to the Domain Administrator in an on-premises AD environment. The Azure AD Global Administrator accounts are the first accounts created so that administrators can begin configuring their tenant and eventually migrate their users. Multi-factor authentication (MFA) is not enabled by default for these accounts. These accounts are exposed to internet access because they are based in the cloud. If the password has been compromised on the Dark Web or elsewhere, these cloud-based accounts could allow an attacker to maintain a constant presence in a customer’s critical O365 services from the very start of migration – essentially giving them the keys to the kingdom. Solution: Ensure that multi-factor authentication is enabled from the beginning of your migration to the cloud. If you are unsure how to do this, a reliable Managed Service Provider will be able to implement this step. Think Before You Sync Azure AD Connect integrates on-premises environments (non-cloud) with Azure AD when customers migrate to O365 (cloud). This technology provides the capability to create Azure AD identities from on-premises AD identities (or to match previously created Azure AD identities with on-premises AD identities). The on-premises identities then become the authoritative identities in the cloud. In order to match identities, the AD identity needs to match certain attributes. If matched, the Azure AD identity is flagged as on-premises managed. Therefore, it is possible to create an AD identity that matches an administrator in Azure AD and create an account on-premises with the same username. One of the authentication options for Azure AD is “Password Sync.” If this option is enabled, the password from on-premises overwrites the password in Azure AD. In this particular situation, if the on-premises AD identity is compromised, then an attacker could move laterally to the cloud when the sync occurs. Solution: Ensure Azure AD password sync is planned for and configured correctly, prior to migrating users. A knowledgeable Managed Service Provider will be able to guide you through proper implementation of this precautionary measure. Just Following (Legacy) Protocol? Azure AD is the authentication method that O365 uses to authenticate with Exchange Online, which provides email services. It is important to keep in mind that there are several protocols associated with Exchange Online authentication that do not support modern authentication methods with multi-factor authentication features (such as POP3, IMAP and SMTP). Legacy protocols are used with older email clients and can be disabled at the tenant level or at the user level. However, if your organization requires older email clients as a business necessity, these protocols will not be disabled. This leaves email accounts exposed to the internet with only the username and password as the primary authentication method. Given the rampant exposure of credentials on Dark Web markets and elsewhere, a breach is highly likely to follow. Solution: One approach to mitigate this issue is to inventory users who still require the use of a legacy email client and legacy email protocols. Using Azure AD Conditional Access policies can help reduce the number of users who have the ability to use risky legacy protocol authentication methods. Taking this step will greatly reduce the attack surface for organizations. Again, an experienced Managed Service Provider will be able to ensure that your business is using the proper protocols. ID Agent provides a robust suite of services to address the risks faced by MSPs and that of their SMB clients. BullPhish ID™ delivers security awareness training and phishing simulations created specifically to help employees recognize and avoid phishing traps. Dark Web ID™ monitors the dark web for employee and supply chain credential exposure, which most often results from using those credentials on third-party websites. SpotLight ID™ provides comprehensive personal identity protection and restoration services for employees and customers, mitigating risk and providing peace of mind.
Read More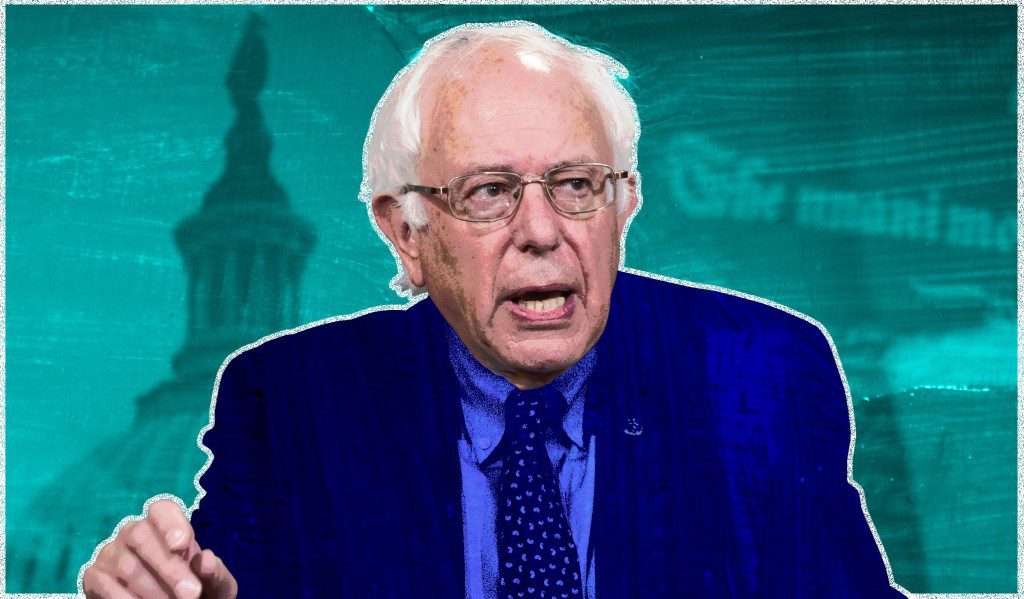
The future of community organizing or the latest flagrant violation of online privacy? That’s the debate currently raging over the Bernie Sanders presidential campaign’s roll-out of its new “BERN” application. The campaign positions it as a new organizing tool that assists volunteers in tracking potential supporters – permitting them to log the name and background of anyone they talk to: from friends and family members to complete strangers on the street. But skeptics argue that the database of personal information could open non-supporters up to harassment. While a sizable proportion of the data the app requests is publicly available for savvy political operatives who know where to look, critics say that having the data neatly compiled — while not giving people a way to opt out of it — presents online and offline safety concerns. So how did this hotly debated application expose private information of up to 150,000,000 American voters? It seems that an error in the app’s source code caused personal voter identification numbers to be exposed for several hours before ultimately being corrected. Visitors to the website could simply use the F12 Developer Tools shortcut to inspect HTML elements, displaying results like this: (personal information redacted to protect user privacy) Defenders of the application note that information like this has long been accessible by campaigns through the use of CRM tools like NGP VAN and others. However, opponents argue that there are some important caveats. Traditionally, campaign staff using the above tools are limited to data about the precincts they work in, data packets are coded, and personnel are monitored – the BERN app contained no such restrictions. Publishing voter files online is illegal in every state – and for good reason. In some states, voter ID numbers are identical to other identifying numbers like those found on Driver’s Licenses or Social Security cards. This is deeply troubling as hackers and criminals could use these legitimate records to make counterfeit IDs and subsequently use them to open bank accounts and commit other types of fraud. Setting aside critical identifiers like Social Security numbers, the exposed information such as a user’s age, residence, gender, zip code and other “banal” data can be cross-referenced with personal records already compromised on the Dark Web. For example, a cybercriminal typically purchases stolen credit card information on the Dark Web for less than $10 per record. To carry out an online purchase, a hacker would have to know your address and ZIP code – and thanks to the BERN leak, this information is already out there. For in-store purchases, a hacker could simply clone your credit card and, in the rare case that a store associate asks for a photo ID, use the Driver’s License number found on BERN to create a convincing and scannable counterfeit ID. (sample Dark Web advertisement for stolen credit card information) So how do you protect yourself from becoming a victim of identity theft? Organizations have proved time and time again that they are unable to ensure complete security of your personal information; therefore, it would benefit private citizens to enroll in an Identity Monitoring service. By enlisting the help of a trusted provider, online users can monitor their credit cards, driver’s license, Social Security number, medical records and even their passwords – and be alerted when they are for sale on the Dark Web, the world’s largest marketplace for stolen information. ID Agent provides a robust suite of services to address the risks faced by MSPs and that of their SMB clients. BullPhish ID™ delivers security awareness training and phishing simulations created specifically to help employees recognize and avoid phishing traps. Dark Web ID™ monitors the dark web for employee and supply chain credential exposure, which most often results from using those credentials on third-party websites. SpotLight ID™ provides comprehensive personal identity protection and restoration services for employees and customers, mitigating risk and providing peace of mind.
Read More
***SPOILER ALERT: this article contains some plot details up to Season 8, episode 2*** The epic struggle of Jon Snow, Daenerys Targaryen and their fragile coalition of allies against the looming undead army of White Walkers bears a striking resemblance to the growing specter of cyberthreats against small to medium sized businesses in recent years. So how do you make people care about cybersecurity as much as they care about who will reign supreme over Westeros? Simple – frame these threats in the fantastical terms they already understand from Sunday nights watching HBO. Westeros as an SMB Westeros, the fictional continent where much of the show’s action takes place, is an excellent metaphor for your organization’s IT environment. It has a clear perimeter as an island surrounded by water and contains significant assets – food, weapons, livestock, infrastructure and its citizens (just as a business owns personal data, payment information, intellectual property and other sensitive material). While there is some warring between the Lannisters, Starks and other houses, it’s helpful to think of them as various departments within the same organization – jockeying for resources, much as different business units might fight for limited budget. A united Seven Kingdoms allows us to recognize the true existential threat to the security and prosperity of Westeros’s inhabitants – the White Walkers. The most direct cybersecurity parallel to this horde of undead would be a malware botnet. A botnet is a collection of internet-connected devices such as computers, smartphones or IoT devices whose security has been breached and control ceded to a third party (the ice-cold third party being The Night King in this scenario). Much like The Night King is able to raise his victims from the dead to join his ranks, hackers are able to fool unsuspecting users by implanting and executing malware on their devices, oftentimes through advanced phishing attacks, to take control of them. This malware could restrict access to business-critical systems for a ransom and harvest user credentials to grant hackers access to financial resources — two techniques that could potentially bankrupt an SMB. The hacker can also use infected devices to carry out ever larger-scale attacks, such as Distributed Denial of Service (DDoS) attacks against your website. As we learned in the latest episode of Game of Thrones, The Night King is seeking to launch a DDoS attack on Westeros and beyond, with the goal of permanently shutting down the living. Another similarity that Game of Thrones superfans will appreciate: neither the White Walkers nor hacking tools were originally conceived with destructive purposes in mind. The White Walkers were originally human-like figures created with magic by the Children of the Forest to protect them from the First Men. They were defense weapons created with good intentions that eventually became so powerful, they threatened all of humanity. Similarly, cyberweapons like StuxNet were originally developed as tools of defense to limit the advances of Iran’s nuclear program, but have since fallen into the hands of third-party criminal groups, who continue to leverage the techniques that made StuxNet possible. Speaking of hacking tools that were previously only available to national governments but are now utilized by criminals, the White Walkers currently have access to more powerful resources than ever before – namely, a terrifying ice-fire-breathing dragon. This parallels the now widespread use of tools like those released by The Shadow Brokers in 2016. The exploit EternalBlue, developed by the NSA in the name of national security and leaked by The Shadow Brokers, was used in the infamous worldwide WannaCry attack that affected over 200,000 computers across 150 countries. Similar to the defense measures that many SMBs implement, Westeros has indeed taken steps to protect itself from the murderous throngs of ice zombies to their north. The most notable example of this would be The Wall. 300 miles long, 700 feet tall and fortified with ancient magic, this rock-solid ice wall could most easily (and ironically) be compared to a Firewall. It’s the first line of defense against intruders, and it takes a Night’s Watch of IT Administrators to maintain it, guard it and analyze for vulnerabilities. As any cybersecurity professional knows, a firewall is a significant defense but can be bypassed by a savvy hacker who knows how to exploit human error, compromised credentials and unpatched applications (or in GoT, by a savvy zombie sociopath with a seemingly unstoppable ice dragon). How to fight back So what can be done to keep your digital kingdom safe? First, you want to make sure your organization’s leadership isn’t like Cersei Lannister – Queen of the Seven Kingdoms who is unwilling to address the existential threat from the North. Much like the wise Maesters of the Citadel, you’ll need to educate decision-makers about the consequences of inaction. For example, 60% of SMBs go bankrupt within the first 6 months following a major cyber incident. Because the vast majority of data breaches are due to human vulnerability and compromised credentials, you’ll want to focus on cybersecurity best practices; these practices are your weapons forged from dragon-glass and Valyrian steel – the only ones proven to be effective against White Walkers. Just as Arya Stark is lethally trained by the Faceless Men, make sure your employees are trained to recognize phishing attempts that may contain malicious files or requests. You’ll also want your very own Three-Eyed Raven. That’s to say, you will want to implement a Dark Web Monitoring service to detect when your users’ credentials are compromised on the Dark Web. Leveraging visibility of your business’s weak spots will give you a *Stark* advantage against hackers (pun very much intended). Be sure to implement strong password phrases and modify them on a regular basis. Lastly, enlist the help of a dragon of your own. Managed Service Providers are a powerful resource for SMBs, armed with knowledge and experience in fighting off cybercriminals. A reputable MSP who focuses on the above techniques like Security Awareness Training and Dark Web Monitoring will be a fiery champion for your digital realm. ID Agent provides a robust suite of services to address the risks faced by MSPs and that of their SMB clients. BullPhish ID™ delivers security awareness training and phishing simulations created specifically to help employees recognize and avoid phishing traps. Dark Web ID™ monitors the dark web for employee and supply chain credential exposure, which most often results from using those credentials on third-party websites. SpotLight ID™ provides comprehensive personal identity protection and restoration services for employees and customers, mitigating risk and providing peace of mind. Send us a raven to schedule a demo today!
Read More