“BERN” App Divulges 150 Million Voter Records
The future of community organizing or the latest flagrant violation of online privacy? That’s the debate currently raging over the Bernie Sanders presidential campaign’s roll-out of its new “BERN” application.
The campaign positions it as a new organizing tool that assists volunteers in tracking potential supporters – permitting them to log the name and background of anyone they talk to: from friends and family members to complete strangers on the street. But skeptics argue that the database of personal information could open non-supporters up to harassment. While a sizable proportion of the data the app requests is publicly available for savvy political operatives who know where to look, critics say that having the data neatly compiled — while not giving people a way to opt out of it — presents online and offline safety concerns.
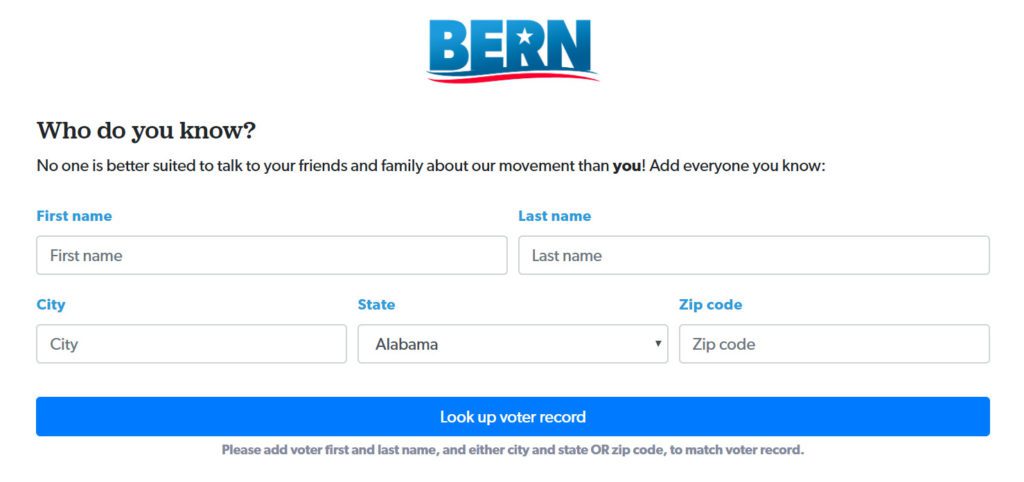
So how did this hotly debated application expose private information of up to 150,000,000 American voters? It seems that an error in the app’s source code caused personal voter identification numbers to be exposed for several hours before ultimately being corrected. Visitors to the website could simply use the F12 Developer Tools shortcut to inspect HTML elements, displaying results like this:
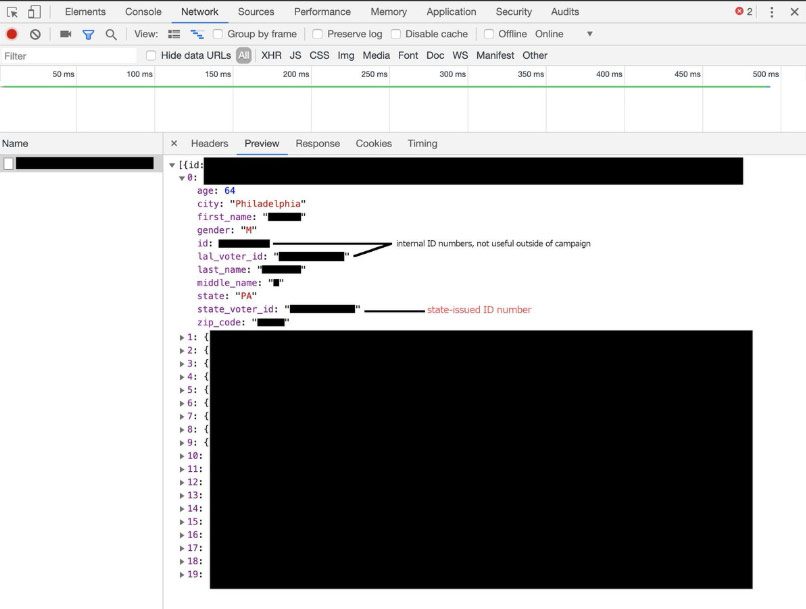
Defenders of the application note that information like this has long been accessible by campaigns through the use of CRM tools like NGP VAN and others. However, opponents argue that there are some important caveats. Traditionally, campaign staff using the above tools are limited to data about the precincts they work in, data packets are coded, and personnel are monitored – the BERN app contained no such restrictions.
Publishing voter files online is illegal in every state – and for good reason. In some states, voter ID numbers are identical to other identifying numbers like those found on Driver’s Licenses or Social Security cards. This is deeply troubling as hackers and criminals could use these legitimate records to make counterfeit IDs and subsequently use them to open bank accounts and commit other types of fraud.
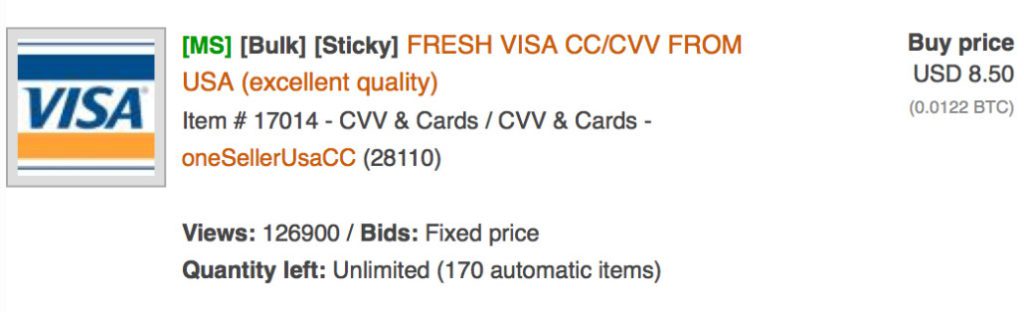
Setting aside critical identifiers like Social Security numbers, the exposed information such as a user’s age, residence, gender, zip code and other “banal” data can be cross-referenced with personal records already compromised on the Dark Web. For example, a cybercriminal typically purchases stolen credit card information on the Dark Web for less than $10 per record. To carry out an online purchase, a hacker would have to know your address and ZIP code – and thanks to the BERN leak, this information is already out there. For in-store purchases, a hacker could simply clone your credit card and, in the rare case that a store associate asks for a photo ID, use the Driver’s License number found on BERN to create a convincing and scannable counterfeit ID.
So how do you protect yourself from becoming a victim of identity theft? Organizations have proved time and time again that they are unable to ensure complete security of your personal information; therefore, it would benefit private citizens to enroll in an Identity Monitoring service. By enlisting the help of a trusted provider, online users can monitor their credit cards, driver’s license, Social Security number, medical records and even their passwords – and be alerted when they are for sale on the Dark Web, the world’s largest marketplace for stolen information.
ID Agent provides a robust suite of services to address the risks faced by MSPs and that of their SMB clients. BullPhish ID™ delivers security awareness training and phishing simulations created specifically to help employees recognize and avoid phishing traps. Dark Web ID™ monitors the dark web for employee and supply chain credential exposure, which most often results from using those credentials on third-party websites. SpotLight ID™ provides comprehensive personal identity protection and restoration services for employees and customers, mitigating risk and providing peace of mind.