
What Is Spoofing? How It Works, Types, Detection & Prevention
Spoofing is a deceptive tactic used by cybercriminals. Understand how it works, different types, and discover solutions that’ll help you combat these threats.
Read More
Spoofing is a deceptive tactic used by cybercriminals. Understand how it works, different types, and discover solutions that’ll help you combat these threats.
Read More
Explore the dangers posed by AI phishing attacks and learn about AI-enhanced defensive tools that can help you mitigate that risk.
Read More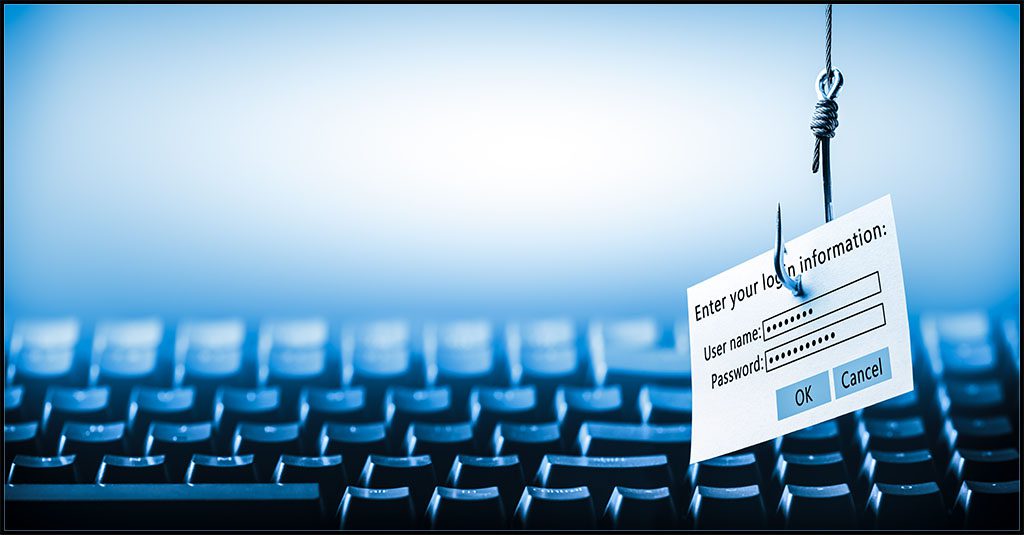
Discover the various types of phishing attack methods and learn effective strategies to safeguard against these prevalent cybersecurity threats.
Read More
A zero-day attack occurs when actors exploit a software or application vulnerability that is unknown to the vendor or developer. Learn how to prevent them.
Read MoreLearn about the similarities and differences between third party risk and supply chain risk with real-life examples.
Read More
Learn why spam isn’t as harmless as you might think and how to mitigate the risk of trouble with the Graphus Personal Spam Filter.
Read More
Learn more about types of third party and supply chain risk and the multiple vectors that businesses face when trying to mitigate it.
Read More
10 tips to help you build an effective security awareness & phishing resistance training program for any organization.
Read More
A malicious insider can do major damage to a company fast. See what motivates malicious insiders & red flags to watch for to detect trouble.
Read More
See how businesses experienced ransomware this year including which data was encrypted and the steps they took to recover if possible.
Read More