A Guide to Navigating NIST 2.0

The recent update to the U.S. National Institute of Standards and Technology’s (NIST) Cybersecurity Framework, commonly referred to as NIST 2.0, marks a significant evolution in the benchmark for cybersecurity practices. NIST has updated their signature framework to reflect the evolution of the cyber threats that organizations face as well as the growing sophistication of, and societal reliance on, digital infrastructure. For businesses, understanding and implementing NIST 2.0 is not just about compliance, but about strengthening their defenses against cyberattacks and improving their overall security posture.

How much is data really worth on the dark web? Find out in The IT Professionals Guide to the Dark Web! GET EBOOK>>
Why is the NIST cybersecurity framework important?
NIST‘s mission is to promote U.S. innovation and industrial competitiveness by advancing measurement science, standards and technology. The NIST Cybersecurity Framework is designed to help businesses and information technology professionals navigate the complexities of cybersecurity. It aims to help stakeholders understand, manage and reduce their cybersecurity risk as they strive to protect their networks and data from evolving cyber threats. Utilizing the framework gives businesses an outline of cybersecurity best practices and guidance to help decision-makers determine where to spend money on cybersecurity.
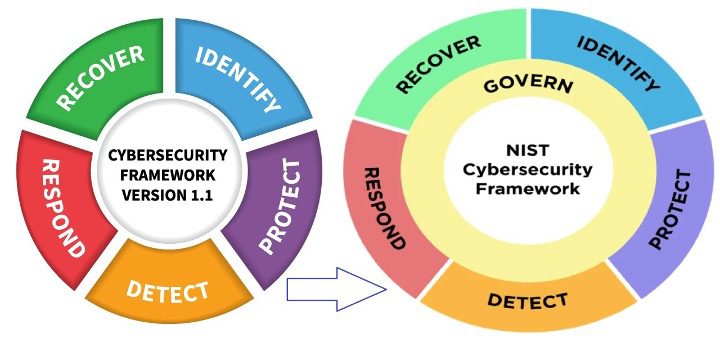
Compliance with a cybersecurity framework is also a great way to show business partners that a company is serious about cybersecurity. It may also be a requirement in some regulated industries. The original NIST Cybersecurity Framework concentrated on five areas: Identify, Protect, Detect, Respond and Recover. But the rapid evolution of the cyber threat landscape has left the old framework a little threadbare, necessitating a retooling.
What is NIST 2.0?
NIST 2.0 is an update to the original NIST framework that is designed to provide an updated standard for improving cybersecurity in the face of today’s sophisticated threats. It is intended to be implemented by private sector organizations and government agencies alike. NIST 2.0 builds on the original version by emphasizing adaptability, highlighting new security technologies and addressing complex cybersecurity challenges.

Source: NIST
Key updates in NIST 2.0
- Increased focus on supply chain security: NIST 2.0 introduces more comprehensive guidelines for managing cybersecurity risks within the supply chain. This is crucial in today’s interconnected business environments where third-party services and products can introduce vulnerabilities. In our Kaseya Security Survey Report 2023, we noted that the majority of our survey respondents (61%) said their organization has experienced a cyberattack through their supply chain or a third-party service provider.
- Emphasis on cyber resilience: Unfortunately, it’s a sad reality that businesses are highly likely to fall victim to a cyberattack. In the Kaseya Security Survey Report 2023, 78% of respondents said they believe they’ll be hit by phishing in the next year, and 58% of respondents think it’s likely they’ll be hit by ransomware in the next 12 months. The updated framework stresses not only preventing cyberattacks but also preparing for, responding to and recovering from them. It guides organizations on how to continue operations despite successful attacks, thereby reducing potential downtime and losses.
- Integration of privacy controls: Recognizing the overlap between privacy and cybersecurity, NIST 2.0 integrates privacy controls into the framework. This helps organizations address privacy risks in digital products and services alongside security risks.

Learn to defend against today’s sophisticated email-based cyberattacks DOWNLOAD EBOOK>>
3 ways this impacts business cybersecurity
NIST 2.0 is sure to have reverberations that spread through the technology world. Here are three ways that businesses may be impacted by the changes.
- Improved risk management: NIST 2.0 offers a more dynamic approach to risk management, encouraging businesses to adapt their cybersecurity practices based on evolving threats and business needs. This is essential for maintaining robust security in a landscape where threats continually evolve.
- Better resource allocation: By prioritizing and streamlining cybersecurity efforts, NIST 2.0 helps businesses allocate their resources more effectively. Companies can focus on high-risk areas and ensure that their cybersecurity investments deliver the greatest impact.
- Enhanced compliance and trust: For businesses in regulated industries, adopting NIST 2.0 can simplify compliance with various cybersecurity regulations. Moreover, demonstrating adherence to a recognized framework can enhance trust among customers and partners.

Learn how to spot today’s most dangerous cyberattack & get defensive tips in Phishing 101 GET EBOOK>>
Key changes and features
- Expanded scope: CSF 2.0 has broadened its focus to support a wider range of organizations, moving beyond its original emphasis on U.S. critical infrastructure. This change addresses the global adoption of the framework and acknowledges the diverse cybersecurity needs of different organizations.
- Introduction of a new function – Govern: One of the notable changes in CSF 2.0 is the addition of a sixth function, “Govern,” to the existing functions of Identify, Protect, Detect, Respond, and Recover. This new function focuses on governance, emphasizing the strategic management of cybersecurity risks and the integration of cybersecurity into overall business governance.
Source: NIST
- Enhanced guidance on implementation: CSF 2.0 offers improved guidance and resources to help organizations tailor the framework to their specific needs. This includes quick-start guides, implementation examples, and a CSF 2.0 Reference Tool that simplifies the adoption and application of the framework. The reference tool allows users to browse, search, and export data and details from the framework’s core guidance in formats that are easy to consume.
- Support for diverse organizational needs: The updated framework provides pathways for various types of organizations to implement the CSF according to their unique circumstances. This includes detailed guidance for sectors such as small businesses and enterprise risk managers, focusing on practical and effective adaptations of the framework’s core principles.
Implementing NIST 2.0
To effectively implement NIST 2.0, businesses should:
- Conduct a gap analysis: Assess current cybersecurity practices against the NIST 2.0 guidelines to identify areas for improvement.
- Develop a tailored implementation plan: Based on the gap analysis, create an actionable plan that addresses identified weaknesses and leverages existing strengths.
- Engage all levels of the organization: Cybersecurity is a company-wide responsibility. Training and engaging employees at all levels ensures that they understand their roles in maintaining security.
- Regularly review and update: Cybersecurity is not a one-time effort. Regular reviews and updates to the cybersecurity strategy as per NIST 2.0 guidelines will help businesses stay aligned with the best practices and emerging threats.
NIST 2.0 is more than just a compliance requirement; it’s a strategic asset that can significantly enhance an organization’s cybersecurity measures. By adopting and adapting the NIST 2.0 framework, businesses can not only protect themselves from the increasing threat of cyberattacks but also enhance their operational resilience and build trust with stakeholders. As cyberthreats evolve, so too should the strategies to combat them. NIST 2.0 provides the roadmap for businesses to navigate this complex and ever-changing landscape.

Explore the nuts and bolts of ransomware and see how a business falls victim to an attack. GET EBOOK>>
Kaseya’s security suite helps businesses mitigate all types of cyber-risk affordably
Kaseya’s Security Suite has the tools that MSPs and IT professionals need to mitigate cyber-risk effectively and affordably, featuring automated and AI-driven features that make IT professionals’ lives easier.
BullPhish ID — This effective, automated security awareness training and phishing simulation solution provides critical training that improves compliance, prevents employee mistakes and reduces a company’s risk of being hit by a cyberattack.
Dark Web ID — Our award-winning dark web monitoring solution is the channel leader for a good reason: it provides the greatest amount of protection around with 24/7/365 human and machine-powered monitoring of business and personal credentials, including domains, IP addresses and email addresses.
Graphus — Automated email security is a cutting-edge solution that puts three layers of AI-powered protection between employees and phishing messages. It works equally well as a standalone email security solution or supercharges your Microsoft 365 and Google Workspace email security.
RocketCyber Managed SOC — Our managed cybersecurity detection and response solution is backed by a world-class security operations center that detects malicious and suspicious activity across three critical attack vectors: endpoint, network and cloud.
Datto EDR — Detect and respond to advanced threats with built-in continuous endpoint monitoring and behavioral analysis to deliver comprehensive endpoint defense (something that many cyber insurance companies require).
Vonahi Penetration Testing – How sturdy are your cyber defenses? Do you have dangerous vulnerabilities? Find out with vPenTest, a SaaS platform that makes getting the best network penetration test easy and affordable for internal IT teams.
Learn more about our security products, or better yet, take the next step and book a demo today!