How Can Businesses Overcome the Cybersecurity Talent Shortage?

These three tips can help businesses maneuver through the cybersecurity talent shortage
In recent years, the cyberthreat landscape has evolved immensely. Organizations in all sectors are dealing with a constant barrage of cyberattacks. At the same time, businesses are struggling to recruit the right talent to protect their systems and data against cybersecurity threats. With cybercrime now accounting for billions of dollars in yearly losses, the need for proficient cybersecurity professionals has never been greater, but the number of workers available to fill those jobs hasn’t grown enough to keep up, leaving businesses in the lurch. But there are a few ways that businesses can overcome the challenge and put strong security in place without the burden of hiring new personnel.

Explore SMB cybersecurity pain points and spending plans in the Datto SMB Cybersecurity for MSPs Report. READ IT>>
How serious is the cybersecurity talent shortage?
While the global cybersecurity workforce stands at 4.7 million, the labor shortage in the cybersecurity industry is only worsening, according to the Cybersecurity Workforce Study by the International Information System Security Certification Consortium (ISC)². The report states that the global cybersecurity workforce gap has increased by 26.2% compared to 2021, with 3.4 million more workers needed for effective cybersecurity practices. In the U.S. alone 7736 cybersecurity job openings were listed between October 2021 and October 2022. More than two-thirds of the total 11,779 respondents in the study reported that their organization lacks cybersecurity employees. Almost half of the respondents predicted that staff deficits put their organization at a moderate to extreme risk of a cyber incident.
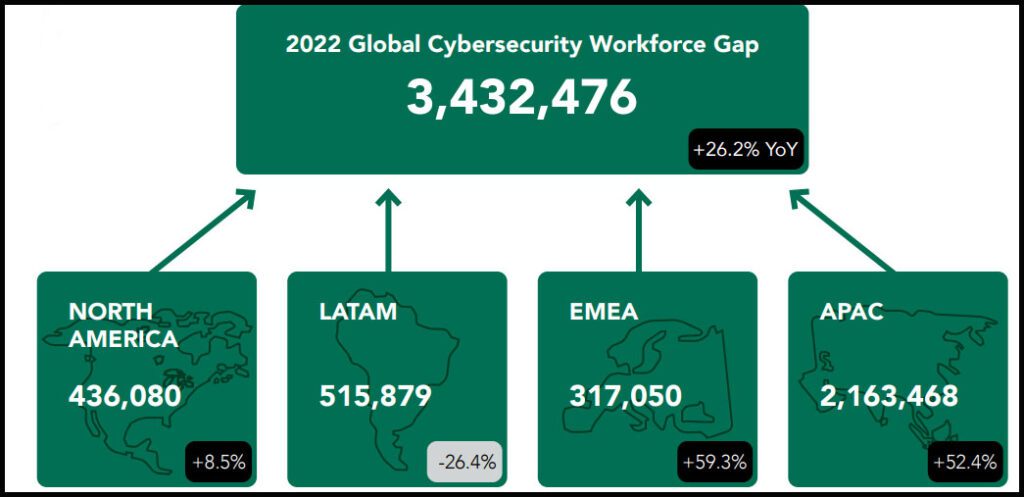
Source: (ISC)2
Why does this workforce gap exist?
Why is it so hard to hire cybersecurity workers? One reason is the difficulty that prospective workers find in obtaining the specialized training and education required to work in the field. Cybersecurity encompasses a broad range of skills and work roles. Certain knowledge and skillsets are fundamental, including understanding computer architecture, administration, and management of operating systems (Linux, Windows, etc.), networking and virtualization software. Plus cybersecurity professionals need to have a deep understanding of specialized things like cyberattack methodology, firewalls, network security controls and mitigation techniques. But a “cybersecurity certification”doesn’t mean that the worker has all of those skills since the industry lacks standardization in testing and certification requirements.
Although organizations need professionals with deep technical training who can take on high-value cybersecurity roles, many technology-focused job training programs don’t offer a cybersecurity track or adequate training in cybersecurity. Plus, finding an affordable cybersecurity-focused training program can be difficult for prospective workers and career switchers. Cybersecurity is also not commonly a focus of secondary school technology courses, especially in challenged areas without STEM learning opportunities. Efforts like (ISC)2’s One Million Certified in Cybersecurity program, which offers education and certification for the (ISC)2 Certified in Cybersecurity certification for free to a million people, have attempted to fill the gap but they’ve barely scratched the surface of the problem.

What worries security pros? The Kaseya Security Insights Report 2022 tells you. GET YOUR REPORT>>
3 tips for addressing the cybersecurity skills gap
These three tips can help businesses solve the cybersecurity talent shortage problem
- Many businesses are finding it prudent to develop their cybersecurity specialists in-house through a combination of training and experience. An organization can avoid a long and expensive hiring process by training employees interested in moving into cybersecurity-focused roles in areas like penetration testing, secure system design, network architecture, security monitoring and incident response. This is particularly helpful for large companies. Only 49% of companies with more than 1000 employees who had implemented all three of (ISC)2’s internal training recommendations had staffing shortages compared to 77% of those who had implemented none.
- Security automation is another tool that can help organizations address the labor and skill gap. Organizations can help their workforce spend more time on productive tasks by automating their repetitive and time-consuming tasks. Automated security solutions like AI-powered email security are also more effective than humans. Innovation has made automated security solutions affordable for most businesses.
- Outsourcing some or all of the company’s security needs can bridge the gap and often provides companies with better security than they could afford if they developed a team in-house. By choosing a managed Security Operations Center (SOC) or managed detection and response (MDR), businesses gain the benefit of having cybersecurity experts on hand detecting and solving security problems before they become disasters 24/7 without hiring anyone or investing in hardware and software. As an added bonus, with a managed SOC businesses have invaluable expertise on call for incident response in the event that they do experience a cyberattack.

See how security awareness training stops the biggest security threats! GET INFOGRAPHIC>>
Managed SOC helps keep organizations safe from cyber threats without expanding the payroll
Managed SOC
Our innovative and affordable Managed SOC gives you access to an elite team of security veterans that hunt, triage and work with your team when actionable threats are discovered as well as a host of other benefits that come from MDR.
- Detect malicious and suspicious activity across three critical attack vectors: Endpoint, Network & Cloud
- Real-time monitoring of malicious and suspicious activity, identifying indicators such as connections to terrorist nations, unauthorized TCP/UDP services, backdoor connections to C2 servers, lateral movements and privilege escalation.
- Patent-pending cloud-based technology eliminates the need for on-prem hardware
- Secure the cloud with Microsoft 365 security event log monitoring, Azure AD monitoring, Microsoft 365 malicious logins and overall Secure Score
- Aligns with Mitre Attack, producing a forensic timeline of chronological events to deter the intruder before a breach occurs.
- Discover adversaries that evade traditional cyber defenses such as Firewalls and AV
Schedule a demo of Managed SOC

Read case studies of MSPs and businesses that have conquered challenges using Kaseya’s Security Suite. SEE CASE STUDIES>>