The Week in Breach News: 05/31/23 – 06/01/23

This week: Cl0p exploited a zero-day flaw in MoveIt to steal payroll data from British Airways, Boots and more UK companies. Toyota has a second data security incident in as many weeks and eight affordable technologies that can mitigate email-based cyberattack risk.

Enzo Biochem
Exploit: Ransomware
Enzo Biochem: Biotechnology Company

Risk to Business: 1.886 = Severe
New York-based biotechnology company Enzo Biochem has disclosed that a ransomware attack in April 2023 has led to sensitive data exposure for millions of patients. Enzo Biochem produces DNA-based tests to detect viral and bacterial diseases, including COVID-19 and cancer. In an SEC filing, the company said that sensitive data including the clinical test information of 2,470,000 individuals and approximately 600,000 Social Security numbers was snatched by the unnamed ransomware group. An investigation is ongoing and no details about any ransom demand were available at press time.
How It Could Affect Your Customers’ Business: Phishing is the number one source for data loss and the most likely way for a company to encounter ransomware.
Kaseya to the Rescue: Learn more about defending against often email-based cyberattacks like ransomware in our eBook A Comprehensive Guide to Email-Based Cyberattacks GET EBOOK>>
Hillsborough County Supervisor of Elections
https://www.baynews9.com/fl/tampa/news/2023/06/01/data-breach-may-impact-58-000-hillsborough-voters
Exploit: Hacking
Hillsborough County Supervisor of Elections: Local Government Agency

Risk to Business: 1.876 = Severe
The Hillsborough County Supervisor of Elections in Florida is informing an estimated 58,000 voters that their personal information may have been stolen in a recent cyberattack. A spokesperson for the agency said that a bad actor illegally accessed and copied files containing voters’ personal identification information, including Social Security and driver’s license numbers. officials were quick to reassure voters that the county’s voter registration system and the ballot tabulation system were not accessed. State and federal agencies are assisting in the investigation.
How It Could Affect Your Customers’ Business This is a worrisome data loss incident at an agency that handles highly sensitive data like voting data.
Kaseya to the Rescue: Develop an effective, efficient incident response plan with the tips in our guide How to Build an Incident Response Plan. GET YOUR GUIDE>>
iSpace
https://www.jdsupra.com/legalnews/ispace-inc-files-notice-of-data-breach-2958304/
Exploit: Hacking
iSpace: Staffing & Business Services Company

Risk to Business: 2.769 = Moderate
California staffing company iSpace has filed a data breach notification in Montana. The filing says that iSpace detected suspicious activity within its computer system on February 5, 2023. An investigation revealed that some files containing sensitive consumer information were accessed and copied by an unauthorized individual between January 30, 2023, and February 5, 2023. The stolen data includes an individual’s name, Social Security number, date of birth, diagnosis information, health insurance group/policy number, health insurance information, subscriber number and prescription information.
How It Could Affect Your Customers’ Business: Data like this is still protected health information, and the rules surrounding that don’t just apply to medical centers and insurers.
Kaseya to the Rescue: Learn more about how our Security Suite can help MSPs protect their clients from expensive and damaging cyberattacks and other information security trouble. GET IT>>
Idaho Falls Community Hospital
Exploit: Ransomware
Idaho Falls Community Hospital: Medical Center

Risk to Business: 1.419 = Extreme
A cyberattack at Idaho Falls Community Hospital left medical staff scrambling and forced some ambulances to divert to other medical centers. The attack, which took place last Monday, also impacted nearby Mountain View Hospital, urgent care center Mountain View Redicare and several smaller clinics. Idaho Falls was forced to divert ambulances for several days, and staffers had to resort to pencil and paper charting. The hospital would not comment on whether or not the attack was ransomware or how long they expected it to take to restore normal operations.
How It Could Affect Your Customers’ Business: Hospitals will continue to be prime targets for ransomware attacks because the nature of their business is time sensitive.
Kaseya to the Rescue: Get details about the five most dangerous email-based cyberattacks businesses face today and defensive tips to stay out of trouble in an infographic. GET INFOGRAPHIC>>

Learn about SMB attitudes toward cybersecurity and other growth opportunities for MSPs. GET INFOGRAPHIC>>
Martinique – The Government of Martinique
https://www.databreaches.net/rhysida-ransomware-group-claims-attack-on-martinique/
Exploit: Ransomware
The Government of Martinique: Regional Government

Risk to Business: 1.781 = Severe
A newer ransomware group, Rhysida, has claimed responsibility for a ransomware attack on the government of the island of Martinique. The group claims to have stolen a variety of data and posted a sample of the stolen data on the dark web. Rhysida offered no further information on the size of the data leak or its contents. In a notice on its website, the government said that the attack took place on May 16, 2023, and “heavily disrupted the activities of the community and directly impacted users and partners.” The attack disrupted education at Martinique’s schools at every level and caused difficulty in the payment of social benefits. No specifics were available about any ransom demand at press time.
How it Could Affect Your Customers’ Business: Governments and government agencies of every size around the world have been experiencing elevated ransomware risk.
Kaseya to the Rescue: Explore how security awareness training helps organizations defend against today’s most dangerous cyber threats in this infographic. DOWNLOAD IT>>

Zellis
Exploit: Ransomware
Zellis: Payroll Company

Risk to Business: 1.226 = Extreme
Employees of several major UK companies including British Airways, Boots and the BBC are being informed that their personal information may have been exposed in a ransomware attack on payroll company Zelis. Bad actors were able to leverage a zero-day exploit in popular file transfer system MOVEit made by Progress Software. The Cl0p ransomware group has claimed responsibility for the attack. Zelis has not disclosed which of its clients were impacted by the attack, but some have already come forward. British Airways disclosed that employee data including National insurance numbers, salaries, contact details, sort codes and bank account numbers. Boots said that its staff had been informed that their data may have been compromised including names, surnames, employee numbers, dates of birth, email addresses, the first lines of home addresses, and national insurance numbers. Details from this incident were still emerging at press time.
How it Could Affect Your Customers’ Business: This is the second zero-day exploit involving a file transfer protocol that has wreaked havoc in 2023.
Kaseya to the Rescue: Learn how Datto EDR satisfies most cyber insurance requirements for endpoint protection and endpoint detection and response (EDR). GET INFORMATION>>
Switzerland – Xplain
https://www.barrons.com/news/swiss-administration-hit-by-cyber-attack-18e93078
Exploit: Ransomware
Xplain: IT Services Company

Risk to Business: 2.807 = Moderate
The Play ransomware gang is behind a ransomware attack that has snarled operations for some of Switzerland’s government. The attack on Xplain, an IT company that supplies homeland security solutions, left several Swiss government arms in the lurch including the Swiss army, government agencies the Federal Office for Customs and Border Security (FOCBS) and the Federal Office of Police (Fedpol) as well as several local police forces. Some stolen data has already been released. Xplain said that they have not communicated with the gang and do not intend to pay any ransom. The company stressed that it offers its customers online applications and does not store the applications and data itself.
How it Could Affect Your Customers’ Business: Service providers like this are good sources of valuable data for bad actors
Kaseya to the Rescue: Email is the most likely way for employees to encounter cyberattacks like ransomware. This checklist helps companies strengthen their email security. GET CHECKLIST>>

Find out about five of today’s biggest dark web threats to businesses in this infographic. DOWNLOAD IT>>

Japan – Toyota
https://www.theregister.com/2023/06/05/security_in_brief/
Exploit: Misconfiguration
Toyota: Car Company
Risk to Business: 2.783 = Moderate
Toyota has discovered another misconfiguration incident, following the incident from two weeks ago. In this case, the company said that data pertaining to 260,000 car owners has been exposed due to the flub. exposed data includes in-vehicle device identifiers and mapping data that’s displayed on the car navigation system of customers in Japan. More detailed data including customer names, postal and email addresses, a Toyota-issued customer identifying number and the vehicle’s registration and identifying numbers may have been exposed for an unspecified number of customers in Asia and Oceania.
How it Could Affect Your Customers’ Business: Two security flubs like this in as many weeks is worrisome and could turn off customers.
Kaseya to the Rescue: Security awareness training doesn’t just protect companies from cyberattacks, it also make employees more conscientious about security overall. GET TRAINING TIPS>>

1 – 1.5 = Extreme Risk
1.51 – 2.49 = Severe Risk
2.5 – 3 = Moderate Risk
Risk scores for The Week in Breach are calculated using a formula that considers a range of factors for each incident

How much is data really worth on the dark web? Find out in The IT Professionals Guide to the Dark Web! GET EBOOK>>


3 New Training Courses in BullPhish ID
A trio of fresh training courses has recently been added to BullPhish ID.
Social Media Safety – Users can learn the risks of using social media and how to avoid a social media based cyberattack. (Available in English, Spanish, French, Portuguese, German and Dutch)
How to Protect Credentials Using Multifactor Authentication – Teach users about the importance of protecting their credentials with multifactor authentication to avoid cyberattacks. (Available in English, Spanish, French, Portuguese, German and Dutch)
The Dangers of Password Sharing – Help users learn why you should never share your passwords with anyone.
Learn more about these new courses in the BullPhish ID Release Notes

This infographic helps IT professionals get the most out of a security awareness training solution. DOWNLOAD IT>>

3 Resources to Help You Defend Against BEC
Business email compromise (BEC) is the most expensive cyberattack that a business can endure. These three resources can help IT professionals defend against BEC.
The Comprehensive Guide to Business Email Compromise – Learn all about BEC and how to avoid it in this eBook that details BEC scams and defensive tips. DOWNLOAD IT>>
The Characteristics of a Successful Security Solution – This checklist helps businesses determine if they’re using the right email security solution. It’s great for MSPs to share with their clients! DOWNLOAD IT>>
How AI Enables Graphus to Protect Businesses from Phishing – Protecting businesses from BEC starts with protecting them from phishing. See how Graphus gets the job done better than the competition. DOWNLOAD IT>>
Did you miss… the Datto EDR HIPAA Compliance data sheet? DOWNLOAD IT>>



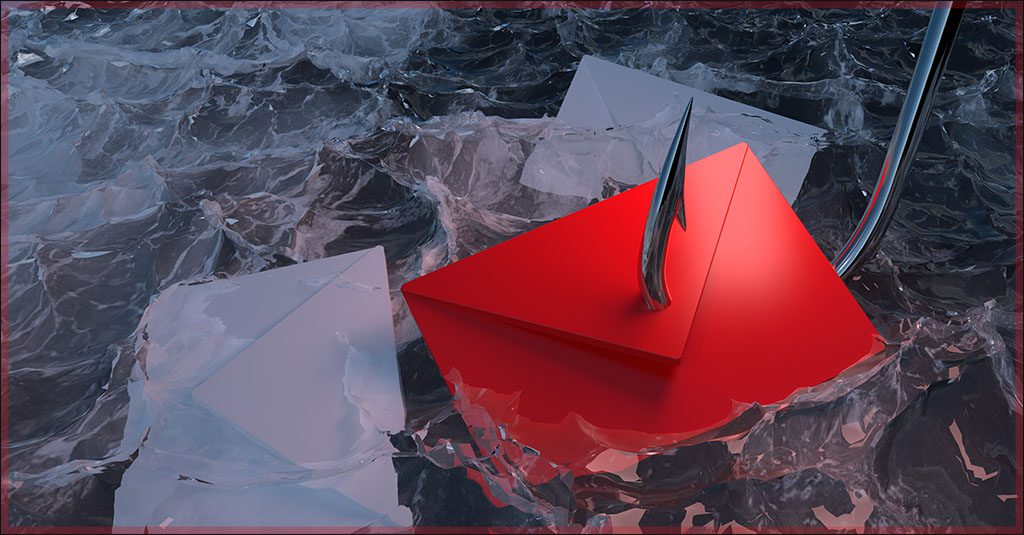
8 Affordable Essential Technologies for Mitigating Email-Based Cyberattack Risk
Email is the most likely vector for an employee to come into contact with a cyber threat. Unfortunately, it’s also the communication channel that businesses use the most, both internally and externally. That gives bad actors plenty of opportunities to strike through email. Email-based cyberattacks are some of the most prolific and devastating cyberthreats organizations face today. Their growing sophistication makes it hard for users to spot dodgy messages as well as more challenging for IT professionals to defend against them. Today’s cybercriminals are constantly innovating new techniques to trick unsuspecting targets. Frequently, that takes the form of social engineering lures disguised to deceive an organizations’ employees, often with catastrophic consequences for systems and data. According to a study, 65% of IT security practitioners cited email as their most significant data loss risk. However, there are a few ways that you can prevent email-based cyberattacks from hitting a business.

Learn how Datto EDR satisfies cyber insurance requirements for endpoint protection & EDR. DOWNLOAD REPORT>>
Email-based cyberattacks are growing more complex
Email-based cyberattacks are the bane of every IT professional’s existence. It only takes one mis click to unleash a massive cyber disaster, making phishing the most prominent threat for organizations of all sizes and across all sectors today. Some of the most expensive and damaging cyberattacks that can impact a business, like business email compromise (BEC), ransomware and account takeover, use phishing as a precursor, and the incidence of those attacks is growing all the time. For example, the number of ransomware attacks recorded in April 2023 was about double the number of ransomware attacks recorded in April 2022. BEC, the most financially damaging cyberattack businesses face, was the cause of an astonishing $2.7 billion in losses last year according to The U.S. Federal Bureau of Investigation Internet Crime Complaint Center (FBI IC3) 2022 Internet Crime Report.
Businesses also face a rising tide of email based cyberattacks through supply chain risk. Bad actors have steadily increased pressure on the global supply chain, with devastating results for companies, especially suppliers, manufacturers and service providers. 90% of global IT leaders believe their suppliers, partners and customers are making their own organization a more attractive target for cyberattacks like ransomware. One big reason that bad actors pursue supply chain attacks is that they think that the security at SMBs may be less stringent than the cyber defense of larger, better-resourced organizations.
Get the scoop on 5 of the worst email-based attacks plus tips to protect businesses from them. GET INFOGRAPHIC>>
Protection from email-based cyberattacks is affordable
Mitigating a company’s risk of falling victim to an email based cyberattack starts with preventing phishing messages from reaching the intended recipients. It doesn’t take a big budget to build a powerful defense against email-based cyberattacks. Ensuring that your security buildout includes these key technologies helps mitigate your risk for all types of cyberattacks, including attacks through email.
Artificial intelligence (AI): AI-enabled email security solutions analyze incoming messages to quickly detect and eliminate threats without human intervention. AI allows a security solution to make judgement calls, reducing administration time and junk alerts.
Automation: Automated email security solutions can stop email-based cyberattacks and quarantine threats before they reach employees without a tech’s support. This reduces the chance of an employee misjudgment and the need to hire more security personnel.

See how security awareness training stops the biggest security threats! GET INFOGRAPHIC>>
Security awareness training: Training is a powerful tool against email-based cyberattacks that use social engineering techniques, reducing the chance that an employee will make a mistake. Organizations that engage their employees in regular security awareness training experience 70% fewer security incidents.
Phishing simulations: Threat actors repeat their successful methods of attack. By simulating phishing threats, you can determine which employees are most likely to fall for a cybercriminal’s lure and keep everyone on the lookout for phishing to mitigate the threat.
Identity and access management (IAM): An IAM solution prevents unauthorized access to your systems and data. Even if a cybercriminal succeeds at phishing a password from an employee, IAM will prevent them from being able to use it to harm your organization. IAM also allows techs to isolate an account quickly if a user account is compromised.
Multifactor authentication (MFA): MFA makes it extremely difficult for cybercriminals to access your systems by requiring users to prove their identity, something a cybercriminal with a freshly phished password likely can’t do. 99% of cyberattacks can be prevented with MFA.
Endpoint Detection and Response (EDR): EDR detects, investigates and advises on threat activity in your endpoints, such as end-user workstations or servers. EDR solutions combine anonymized data and behavioral analysis to protect your organization against existing as well as emerging threats, like a malware infection from an employee clicking a bad link.
Managed Security Operations Center (SOC): A SOC employs a team of experts who monitor your endpoints, network and cloud systems 24/7 and provide managed detection and response. That enables you to make all the right moves if a disaster strikes like an employee downloading a ransomware-laden email attachment. A managed SOC offers you the opportunity to reap the benefits of a SOC without adding any additional hardware or security staff.
EDR and Managed SOC together are a security game changer.
Give email-based cyberattacks the 1-2 punch with Graphus & BullPhish ID
BullPhish ID is a comprehensive and affordable security awareness solution that automates training delivery, testing and reporting, making it the ideal training solution for companies of every size.
- Conduct phishing simulations with pre-loaded phishing kits or customize the content to reflect the unique phishing threats your users face daily and reduce the chance they’ll fall for a phishing-based cyberattack.
- Train with easy-to-understand video lessons about dangers like ransomware, credential compromise and phishing give every employee a solid grounding in cybersecurity best practices with quizzes to determine who needs more help.
- Deliver content seamlessly and track every employee’s progress through their personalized training portal.
Graphus AI-driven, automated email security can help you stay miles ahead of cybercriminals at half the cost of the competition.
- Deployable via API with just three clicks, Graphus instantly starts monitoring communication patterns between people, devices and networks to reveal untrustworthy emails, making it a simple, powerful and cost-effective phishing defense solution for companies of all sizes.
- Put three layers of defense between a phishing email and your organization and automatically prevent 99% of sophisticated phishing messages from reaching an employee’s inbox,
- Gain powerful protection from advanced social engineering and zero-day attacks with Graphus as a stand-alone or combine it with onboard security in Google Workspace or Microsoft 365.
The Drop-a-Phish integration between BullPhish ID and Graphus can help you quickly deploy phishing simulation exercises and security awareness training campaigns by eliminating the need for domain whitelisting. The Graphus API allows BullPhish ID to drop phishing and training emails directly into end-user inboxes, saving hours of whitelisting time and ensuring 100% deliverability of training exercises.
Learn more about the amazing benefits you get from combining Graphus and BullPhish ID here.

Can you spot a phishing message? This infographic points out red flags to watch for to sniff them out! DOWNLOAD IT>>

Learn How to Gain True Protection from Phishing Attacks
A phishing threat can quickly escalate to a disastrous security incident if just one employee falls for scammers’ tricks. Join us on June 13 at 2 PM ET / 11 AM PT for an informative webinar where our Channel Development Manager, Miles Walker, will discuss how you can gain comprehensive protection from phishing attacks with BullPhish ID and Graphus. REGISTER NOW>>
June 8: Kaseya + Datto Connect Local Belgium REGISTER NOW>>
June 8: Kaseya + Datto Connect Local Toronto REGISTER NOW>>
June 13: Kaseya + Datto Connect Local Philadelphia REGISTER NOW>>
June 14: Kaseya + Datto Connect Local Chicago Security for IT Professionals Series REGISTER NOW>>
June 15: Kaseya + Datto Connect Local Chicago Security & Compliance Track REGISTER NOW>>
June 20: Kaseya + Datto Connect Local Tampa REGISTER NOW>>
June 22: Kaseya + Datto Connect Local Atlanta REGISTER NOW>>
June 26-28: Kaseya DattoCon Europe in Dublin REGISTER NOW>>
July 11: Kaseya + Datto Connect Local Anaheim REGISTER NOW>>
July 18: Kaseya + Datto Connect Local Boston REGISTER NOW>>
July 20: Kaseya + Datto Connect Local Baltimore REGISTER NOW>>
July 21: Kaseya + Datto Connect Local Baltimore IT Professionals Series REGISTER NOW>>
October 2 – 4: Kaseya DattoCon in Miami REGISTER NOW>>

Read case studies of MSPs and businesses that have conquered challenges using Kaseya’s Security Suite. SEE CASE STUDIES>>

Do you have comments? Requests? News tips? Complaints (or compliments)? We love to hear from our readers! Send a message to the editor.
Partners: Feel free to reuse this content. When you get a chance, email [email protected] to let us know how our content works for you!