4 Reasons Why Ransomware Risk Won’t Stop Rising for SMBs

Ransomware Risk Isn’t Going Anywhere But Up
Does it seem like ransomware risk and associated costs never stop rising for businesses? That’s because they are rising by leaps and bounds every year. By 2031, a ransomware attack will strike a business every two seconds with an estimated annual cost of $265 billion in damage. This makes ransomware the fastest-growing type of cybercrime. Every business needs to be ready to handle a continuing onslaught of ransomware, and a look at these four factors that are contributing to that constantly growing risk can help ensure that IT professionals are making all the right moves to secure systems and data from this potential disaster.

See cybercrime trends & the results of thousands of phishing simulations in The Global Year in Breach 2022. DOWNLOAD IT>>
Experts Predict Major Ransomware Growth with Skyrocketing Associated Costs
A quick examination of the basic facts about the scope of the ransomware problem that businesses face today shows that the danger of a ransomware disaster is only growing worse for businesses as time goes on. Cybersecurity Ventures estimated the worldwide cost of ransomware at $20 billion in 2021. The number of ransomware attacks that businesses face won’t decrease if it continues to move at the same pace as it has in recent years. In 2020 and 2021, the number of ransomware assaults that organizations endured has more than doubled, increasing by 92.7% year-over-year. Unfortunately, a large number of those assaults are expected to be successful. Analysts at Gartner say that ransomware will have infected 75% of all enterprises by 2025.
A data breach is never cheap, but if a company has a data breach as a result of a ransomware attack they’re looking at even bigger bills. The IBM Cost of a Data Breach 2022 report offers some insight into the prevalence of ransomware-related data breaches, their growing price tag and the damage they can do to a business. It’s probably not a surprise, but the cost of a data breach has reached a new high, reaching $4.35 million this year. That’s a slight jump of 2.6% from the 2021 cost of $4.2 million per incident, which was at the time the highest ever recorded in the 17 years of the study. Many factors influence the cost of a data breach, and the presence of ransomware is one of them. The average cost of a ransomware-related data breach did dip slightly, from $4.62 million in 2021 to $4.54 million in 2022. However, ransomware is still more expensive than other data breaches with an average cost of $4.54 million, 19% higher than the average, not including any ransom paid.
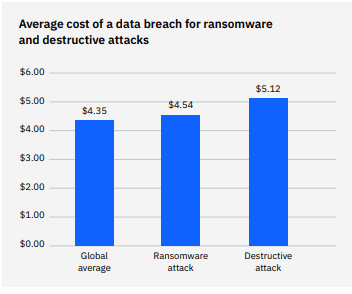
Source: IBM

Get 10 tips to help you build a strong security culture & reduce your risk of cybersecurity trouble! GET INFOGRAPHIC>>
A Major Increase in Email & Phishing Volume Sends Ransomware Risk Soaring
One reason for that difficulty is explosive growth is the most common attack vector for ransomware: phishing. Phishing is a never-ending scourge on businesses, hitting an all-time high in Q1 2022 when researchers recorded more than 1 million attacks in a single quarter for the first time. That’s 1 million potential cyberattacks that could be headed for businesses. The top data breach threat for three consecutive years, phishing is a plague on organizations. 80% of IT professionals saw a substantial increase in phishing attacks including those carrying ransomware in 2021. Consistently rising email volumes from remote work and shifts to more cloud-based operations for businesses give cybercriminals more chances to get phishing messages that carry ransomware into employee inboxes. Far too often, humans unwittingly help attackers gain a foothold in company networks or devices because they fall victim to the lure of a phishing email. An estimated 97% of employees in a wide array of industries are unable to recognize a sophisticated phishing email.
Email Volumes in Billions Estimated
| 2017 | 269 |
| 2018 | 281 |
| 2019 | 294 |
| 2020 | 306 |
| 2021 | 320 |
Source: Statista

Find the perfect training solution for your clients & your MSP with our MSP-focused buyer’s guide. DOWNLOAD IT>>
Big, Consistent Paydays Encourage More Attacks
A successful ransomware attack can net more for bad actors than just data to sell on the dark web. It can also net the bad guys a straight-up extortion payment. About 52% of organizations hit with a ransomware attack choose to negotiate with the extortionists or simply pay the ransom that is demanded, especially organizations involved in time-sensitive operations or critical infrastructure management. Cybercriminals know this and take advantage of it to score a fat payday. The average ransomware payment climbed 82% from $234,000 in 2020 to a record $570,000 in 2021. Paying extortionists is never a good idea, but it is the route that many companies take to escape a ransomware attack. Unfortunately, paying the bad guys doesn’t always produce the desired results. Less than $234,000 in 2020 to a record 60% of companies that pay the ransom when they’ve been hit by a ransomware attack are able to recover even part of their data, and 39% of companies that pay a ransom never see any of their data again. It is also illegal in many circumstances.
Paying the extortionists may get a company out of the jam it’s in immediately, but it just leads to more attacks down the road, sometimes even from the same gang. In fact, CBS News reported that an estimated 80% of organizations that pay the attackers their ransom demand are attacked again. The UK National Cyber Security Centre (NCSC) blog featured a tale about an unnamed organization that was hit by ransomware and opted to pay off the bad guys. The victim forked over more than $6 million for a decryptor in a ransomware hit. But less than two weeks later, the same attacker returned and re-deployed their ransomware successfully a second time, leaving the company still in trouble and $6 million poorer.

Go inside nation-state cybercrime to get the facts and learn to keep organizations safe from trouble! GET EBOOK>>
How Long Can Your Organization Afford to Shut Down or Endure Other Unpleasant Consequences?
Beyond the ransom, one of the biggest disasters that businesses face if they fall victim to a ransomware attack is a shutdown. Most SMBs that are successfully hit by ransomware will be forced to shut down for some length of time. A report in Tech Republic detailed the results of a survey on how long businesses could survive a ransomware-related shutdown. An estimated 75% of the businesses surveyed said their company would survive only three to seven days following a successful ransomware attack. Digging deeper, 47% of those businesses said that they would survive for only three days, while 28% said that they’d survive for up to seven days.
The damage that businesses suffer from a ransomware attack isn’t quickly or easily overcome. The ripple effect goes on and on. Unitrends researchers determined that for companies that have faced ransomware head-on, data loss (22.34%) and downtime (22.13%) were the most common consequences reported. Rounding out the top five most-cited consequences were reputation damage (15.24%), lost profits (13.57%) and compliance failures (9.39%). All three of these elements keep the expense of a ransomware incident snowballing, creating major danger for the long-term viability of the victimized businesses.
Consequences of a Ransomware Attack
| Downtime | 22% |
| Lost data | 22% |
| Data recovered (paid ransom) | 15% |
| Lost profits | 14% |
| Data lost (paid ransom) | 9% |
| Reputation damage | 7% |
| Compliance failure | 6% |
| Other | 5% |
Source: Unitrends MSP
Be the hero that defeats a company’s security threats to declare victory over cybercriminals! GET THE GUIDE>>
Reduce Ransomware Risk with Security Awareness Training
The most likely ways for ransomware to enter a company’s environment is through the actions of an employee. Falling for a phishing message, downloading a dangerous attachment, clicking a malicious link – any of those employee mistakes is an expressway to an expensive, painful ransomware nightmare. But businesses can quickly and affordably reduce the chance of an employee making a security mistake like those with security awareness training and phishing simulations. In fact, companies that engage in security awareness training have 70% fewer security incidents than companies that don’t. Start taking advantage of that benefit with employee training using the award-winning training solution BullPhish ID.
- Choose from a wide variety of plug-and-play phishing simulations, with new phishing simulation kits added every month.
- Train your way with fully customizable phishing kit content including links and attachments to reflect industry-specific threats.
- Access a huge library of security and compliance training videos with 4 new videos added every month on topics like BEC, CMMC compliance, data handling and more.
- Quickly measure retention and see who needs more help with quizzes and easy-to-read progress reports.
- Security and compliance training videos are available in 7 languages!
- NEW FEATURE! Enjoy a major BullPhish ID enhancement, Advanced Phishing Simulations (Drop-A-Phish), that leverages the power of integration with Graphus to eliminate the need for domain whitelisting and ensure 100% campaign deliverability to end users. LEARN MORE>>

Read case studies of MSPs and businesses that have conquered challenges using Kaseya’s Security Suite. SEE CASE STUDIES>>