The Week in Breach News: 08/10/22 – 08/16/22

An employee’s compromised Google account is to blame for a nasty incident at Cisco, 7-11 is closed by ransomware in Denmark and what you need to know about the recent spate of healthcare cyberattacks

Find the perfect training solution for your clients & your MSP with our MSP-focused buyer’s guide. DOWNLOAD IT>>

Cisco
https://www.theregister.com/2022/08/11/cisco_corporate_network_compromised/
Exploit: Hacking
Cisco: Networking Technology Company

Risk to Business: 2.211 = Severe
Cisco Systems confirmed experiencing a cyberattack in May 2022 that was caused by the compromise of an employee’s Google account, The company’s investigation determined that the attackers obtained details of an employee’s private Google account, which contained passwords synced with Cisco’s web browser. The attackers parlayed that into initial access to Cisco’s VPN. The employee’s credentials were synced through the Chrome browser, where the targeted employee had also stored their Cisco credentials. The Yanluowang ransomware gang has claimed responsibility by publishing files stolen in the incident on its dark web leak site.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How It Could Affect Your Customers’ Business: Insecure or compromised employee credentials can do big damage in a very short span of time.
ID Agent to the Rescue: Our Monsters of Cybersecurity eBook helps you discover and mitigate the killer risks that are lurking around every corner. DOWNLOAD IT>>
PlatformQ
Exploit: Misconfiguration
PlatformQ: Digital Engagement Solutions

Risk to Business: 1.687 = Severe
PlatformQ, a provider of digital engagement solutions for healthcare (PlatformQ Health) and education (PlatformQ Education) sector entities, experienced a data breach after an employee accidentally published a database backup stored in a misconfigured AWS S3 bucket. The data appears to be about marketing the drug Zarex to doctor’s offices and similar places, and PII for healthcare professionals was involved.

Individual Risk: 1.733 = Severe
The leak exposed sensitive information including the full names, personal email addresses, job titles work email addresses, home, work and private phone numbers and National Provider Identifier (NPI) numbers of an estimated 99,000 healthcare professionals
How It Could Affect Your Customers’ Business Employee mistakes and negligence are responsible for more data breaches than any other cause, but training helps fix that.
ID Agent to the Rescue: Learn to build an effective program that reduces cyberattack risk with the guide How to Build a Security Awareness Training Program. DOWNLOAD IT>>
Behavioral Health Group
Exploit: Hacking
Behavioral Health Group: Addiction Treatment Center Operator

Risk to Business: 1.716 = Severe
Behavioral Health Group recently began notifying 197,507 patients that their data was stolen in a December 2021 cyberattack. The opioid treatment provider’s 80 clinics suffered a week of IT outages that disrupted patient care after a cyberattack forced the team to shut down portions of the network. That in turn caused delays for health services like refilling patient medications, a critical part of the recovery process for many addiction treatment patients.

Individual Risk: 1.802 = Severe
The stolen data varied by patient and could include patient names, Social Security numbers, driver’s licenses, passports, biometrics, health insurance information, diagnoses, treatments, prescriptions, dates of service, and medical record numbers. Only patients whose SSNs were compromised will receive free credit monitoring.
How It Could Affect Your Customers’ Business: Medical entities of all sorts have been high on cybercriminal hit lists because they know that it’s a rich and time-sensitive industry.
ID Agent to the Rescue: See the biggest risks that businesses face today and get a look at what cyber threats your clients will be facing tomorrow in The Global Year in Breach 2022. DOWNLOAD IT>>
Acorn Financial Services
https://www.jdsupra.com/legalnews/acorn-financial-services-reports-data-5996771/
Exploit: Phishing
Acorn Financial Services: Financial Planners

Risk to Business: 1.837 = Severe
In April 2022, Acorn Financial Services discovered unusual activity within an employee email account that ultimately led to uncovering a data breach. Acorn says that the incident was kicked off by an employee falling for a phishing email. The company acted to secure the employee’s email account and confirmed that an unauthorized actor has potentially gained access to sensitive customer data. The company has filed data breach notifications and is informing the impacted customers via mail.

Individual Risk: 1.646 = Severe
While the breached information varies depending on the individual, it may include the client’s name, address, date of birth, driver’s license number, financial account number, Social Security number and other account-related information.
How it Could Affect Your Customers’ Business: The financial services sector was the most heavily under seige by ransomware last year, a pattern that continues in 2022.
ID Agent to the Rescue: Get the resources that you need to help you protect clients from complex risks in the Deep Dive Into Cybersecurity Bundle. GET BUNDLE>>
Klaviyo
Exploit: Phishing
Klaviyo: Email Marketing Firm

Risk to Business: 2.284 = Severe
In an interesting twist on the usual data breach incident, email marketing firm Klaviyo suffered a concentrated and specific data breach on August 3, 2022. After gaining access to an employee’s account thanks to a successful phishing attack, bad actors then downloaded marketing lists used by cryptocurrency-related clients for outreach efforts and for Klaviyo product and marketing updates. The threat actor used the internal customer support tools to search for primarily crypto-related accounts and viewed list and segment information for 44 Klaviyo accounts, downloading data from at least 38 accounts.

Risk to Business: 2.284 = Severe
Stolen data includes customers’ names, addresses, email addresses, account profile information and phone numbers. The hackers also downloaded two internal lists used by Klaviyo for product and marketing updates that contain names, addresses, email addresses, and phone numbers.
How it Could Affect Your Customers’ Business Phishing is the most likely way for any organization to open the door to a data breach.
ID Agent to the Rescue See the reasons why an AI-driven automated email security solution is the answer to email security challenges and why you and your clients will love it. DOWNLOAD INFOGRAPHIC>>

See five things that you can do to reduce nation-state cyber threat risk for your clients fast. GET CHECKLIST>>

Bombardier Recreational Products (BRP) Inc.
Exploit: Ransomware
Bombardier Recreational Products (BRP) Inc.: Recreational Equipment Manufacturer

Risk to Business: 1.529 = Severe
BRP, Inc, manufacturer of the Ski-Doo and other all-terrain vehicles, watercraft and snowmobiles, has been hit with a suspected ransomware attack that shut down operations briefly at its plants. This attack may have resulted from exposure by a third-party service provider. After an initial complete closure of manufacturing operations, the company expects its manufacturing sites in Valcourt, Canada, Rovaniemi, Finland, Gunskirchen, Austria and Sturtevant in to resume operations imminently.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business Service disruptions from cyberattacks can cost manufacturers and the companies that they supply a fortune.
ID Agent to the Rescue Gain 3 resources featuring a wealth of knowledge about ransomware and how to keep your clients safe from our Introduction to Ransomware Resource Bundle! DOWNLOAD THE BUNDLE
Union des producteurs agricoles (UPA)
https://www.farms.com/ag-industry-news/hackers-target-quebec-ag-organization-301.aspx
Exploit: Ransomware
Union des producteurs agricoles (UPA): Agricultural Trade Organization

Risk to Business: 2.017 = Severe
Hackers launched a ransomware attack on the Union des producteurs agricoles (UPA) on Sunday, a regional agriculture organization. Bad actors deployed ransomware that paralyzed the network, leaving an estimated 160 UPA employees and 23 UPA client organizations, like the union of grain producers, unable to connect. An investigation is ongoing, and services are expected to be quickly restored.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business Groups like this offer a great opportunity for cybercriminals to snatch profitable and useful data.
ID Agent to the Rescue Learn more about the business of ransomware including how the bad guys get paid and get tips for securing your clients in Ransomware Exposed! DOWNLOAD EBOOK>>

Learn to identify and mitigate fast-growing supply chain risk with this eBook. DOWNLOAD IT>>

Denmark – 7 –11 Stores
https://www.securityweek.com/7-eleven-closes-stores-denmark-after-hacker-attack
Exploit: Hacking
7-11 Stores: Convenience Store Chain

Risk to Business: 1.211 = Extreme
The chain of 7-11 stores in Denmark was forced to shut down after a cyberattack disrupted stores’ payment and checkout systems throughout the country. The attack occurred on August 8th, and all stores remain closed while the company investigates the incident. No word on when they’ll reopen or the nature of the attack, although ransomware is suspected.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business No company can afford to be shut down entirely for days or weeks because of a cyberattack, especially not in retail.
ID Agent to the Rescue Learn how to choose a training solution that will offer you and your clients a high degree of satisfaction in our Security Awareness Training Buyer’s Guide for MSPs. DOWNLOAD IT>>

See cybercrime trends & the results of thousands of phishing simulations in The Global Year in Breach 2022. DOWNLOAD IT>>

1 – 1.5 = Extreme Risk
1.51 – 2.49 = Severe Risk
2.5 – 3 = Moderate Risk
Risk scores for The Week in Breach are calculated using a formula that considers a range of factors for each incident

See how today’s biggest threats may impact your MSP and your customers in our security blogs.
- The Soaring Cost of a Data Breach Leads to Soaring Prices
- How Does Ransomware Impact the Cost of a Data Breach?
- How to Spot Phishing Emails: 10 Phishing Red Flags to Look For
- 2 Factors Make Data Breaches More Expensive
- The Week in Breach News: 08/03/22 – 08/09/22

New Training Videos Are Available in BullPhish ID!
Every month, we add new training videos and fresh phishing kits to BullPhish ID to ensure that you and your customers have access to training around the latest cyber threats and compliance changes. These new training courses are now available on BullPhish ID. Access them via Portal: “Dashboard”> “Training Courses”
- Phishing: Brand Fraud and Spoofing
- Nation-State Cybercrime: Industrial and Infrastructure Targets
- CMMC – What Information is Protected and Why?
Learn more about BullPhish ID or talk to one of our sales experts to start offering this award-winning solution!

Solve five of the most exhausting remote and hybrid security problems fast with this handy infographic! DOWNLOAD IT>>

Help Your Clients Reduce Risk by Building a Strong Cybersecurity Culture
Building a strong cybersecurity culture has so many benefits for your customers, but it can be hard to figure out where to start. These resources can help you learn more about the process of building that security culture and how you can guide your customers to success!
Build A Strong Cybersecurity Culture with BullPhish ID – This webinar will help you learn how to guide your clients into mitigating their biggest risks with security awareness training. WATCH NOW>>
Building a Strong Security Culture Checklist – This checklist will help you start profitable conversations with your clients and determine where they’ve got security flaws that you can help correct! DOWNLOAD NOW>>
Guide to Reducing Insider Risk – Learn more about the ways that employees can negatively impact their company’s security to cause major problems, and how to help customers steer clear of trouble. READ IT>>
Did you miss…? The Global Year in Breach 2022 DOWNLOAD IT NOW>>

Go inside nation-state cybercrime to get the facts and learn to keep organizations safe from trouble! GET EBOOK>>


The Rising Tide of Healthcare Cyberattacks Can Swamp Your Customers
See How Serious the Problem Has Become & What You Can Do About It
A cyberattack on any organization is a problem that can leave businesses looking at big bills, downtime and regulatory trouble. A cyberattack on a healthcare organization is an even bigger problem. Not only will the organization face those unpleasant consequences, but there’s also an added layer of trouble thanks to the impact a cyberattack can have on patient care. Unfortunately, the tide of healthcare cyberattacks is rising again, leaving too many organizations at risk of a dangerous, damaging incident. Elevated risk and continued pressure on the healthcare sector make helping your clients ensure that their healthcare organizations don’t fall victim to a cyberattack mission-critical right now.

Set businesses on the zero trust path with the 6 Tips for Implementing Zero Trust Security infographic! GET IT>>
56% of Healthcare Organizations Have Experienced 1 or More Cyberattacks That Resulted in a Data Breach in the Last Two Years
New information about the impact of cyber attacks on healthcare has just been released in the Cynerio and Ponemon Institute report The Insecurity of Connected Devices in HealthCare 2022. The biggest takeaway is that a shocking 56% of healthcare organizations have fallen victim to a cyberattack in the last 24 months, and those cyberattacks had a serious impact on patient care, especially when ransomware was involved. IoT devices and similar vectors were the focus of the report. However, additional data that was included painted a picture of the cyber threats and complications from cyber threats that healthcare organizations face today.
As any IT professional knows, a cyberattack isn’t a one-and-done affair for any business. Falling victim once can lead companies down a path of expensive mitigation and recovery with lasting effects. It can also enable attackers to perform long-term operations that plant or discover gateways to future attacks. Of the previously noted 56% of organizations analyzed in this report that fell victim to at least one cyber attack in the last 24 months, 82% of them were hit again quickly. A little over one-third of healthcare organizations experienced an average of 4 or more breaches within a two-year period. Ransomware attack rates were roughly equivalent with 43% of respondents having experienced an attack and 76% of those experiencing an average of three or more.
Number of Data Breaches Experienced
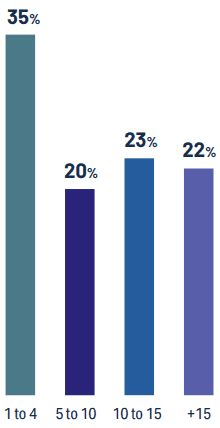
Source: Cynerio

Gain expert insight in the MSP Cybersecurity Roundtable: How Infrastructure Attacks Can Hurt Every Business. WATCH NOW>>
Healthcare Has the Most Expensive Data Breach Cost
This year’s IBM Cost of a Data Breach 2022 report definitively shows that the industry with the highest data breach cost is healthcare. The cost of a data breach at a healthcare organization was almost twice the cost of the number two sector, finance. That cost has been steadily climbing. The average cost of a healthcare data breach jumped almost $1 million in 2022 to a record high of $10.1 million, which is 9.4% more than in 2021 and 41.6% more than in 2020. Pharmaceuticals, a healthcare-related sector, came in third on the list of highest data breach costs. However, organizations in the pharmaceutical sector aren’t paying as much for a data breach in 2022 as it was in 2021. The average total cost of a data breach for pharma companies actually decreased slightly from $5.97 billion in 2021 to $5.72 billion in 2022.
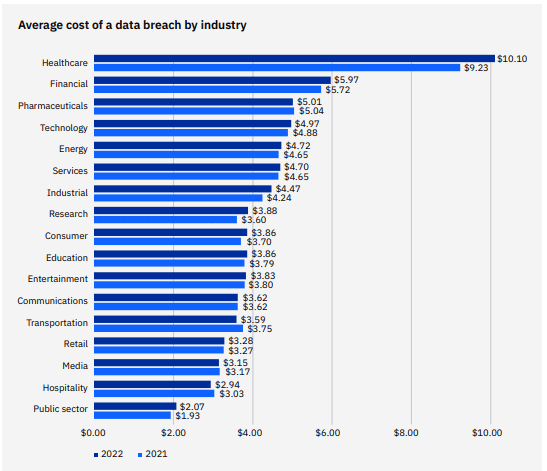
Source: IBM

Can you spot a phishing message? This infographic points out red flags to watch for to sniff them out! DOWNLOAD IT>>
Almost Half of Healthcare Orgs Are Hit by Ransomware
A ransomware attack on any organization is devastating, but a successful ransomware attack can have a far-reaching negative impact in a healthcare setting. Ransomware can cripple a hospital, trauma center or clinic completely. The bad guys are well aware of this, and they haven’t hesitated to take advantage of the additional pressure brought to bear on hospitals by the drawn-out global pandemic to strike healthcare organizations with ransomware in the hope of a quick windfall. Almost half of the healthcare organizations surveyed, 43%, said that they had experienced a ransomware attack in the past 24 months. Digging deeper, researchers determined that more than three-quarters of the healthcare organizations in this study had experienced three or more ransomware attacks within the last 24 months.
Number of Ransomware Attacks Experienced
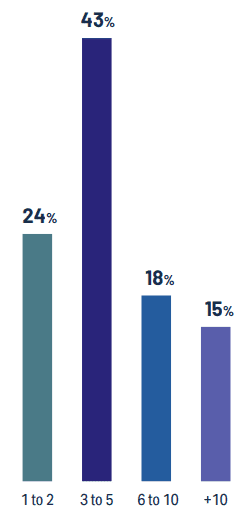
Source: Cynerio

Insider risk is up by 40%. Help your clients stay out of trouble with The Guide to Reducing Insider Risk GET IT>>
Bad Actors Are Mining Gold from Healthcare Attacks
Many hospitals see no choice but to pay the ransom and decrypt their systems and data as quickly as possible before a serious public health crisis results from the ransomware attack. An estimated 47% of healthcare entities that experienced a ransomware attack chose to pay the extortionists, a move that experts classify as a very bad idea that may also be illegal in some cases. On average, 32% of the ransoms paid fall in the range of $250k – $500k. Those that did not pay the ransom most frequently attributed their choice not to pay to an effective backup strategy (53%) and company policy (49%). Unfortunately, this pattern will continue as long as organizations keep shelling out ransom payments that make it profitable for the bad guys.
Ransom Amounts for Healthcare Organizations
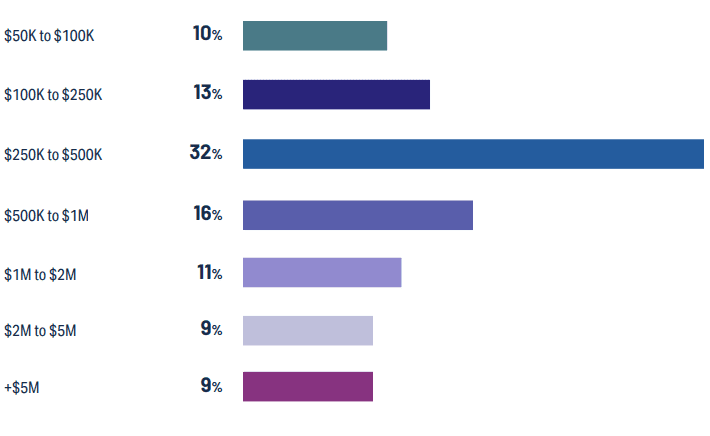
Source: Cynerio

Watch this webinar to learn how to make Dark Web ID your prospecting secret weapon! WATCH NOW>>
Cyberattacks Negatively Impact Patient Care & Mortality Rates
A ransomware attack can complicate operations at a hospital, clinic or specialty care center in many negative ways, including by increasing mortality rates. Almost one-quarter of ransomware attacks that medical care facilities have experienced in the last two years have resulted in a dangerous bump up in mortality rates. Simply put, ransomware can kill people. Ultimately, researchers determined that almost half of cyberattacks on healthcare organizations resulted in an adverse impact on patients, a figure that everyone should find alarming.
Adverse Impacts of a Successful Cyber Attack on Patient Care
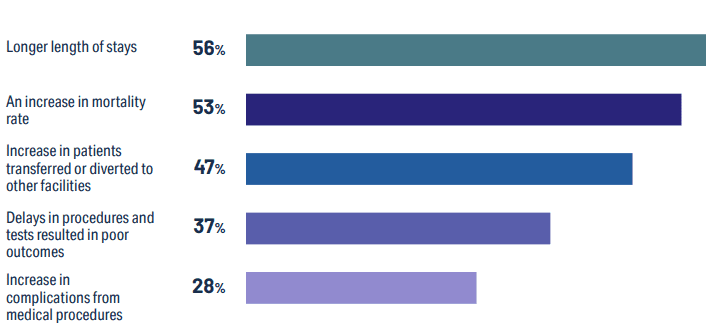
Source: Cynerio

Learn the secret to conjuring up amazing stress-free marketing campaigns in 5 Ways to Make Marketing Magic! GET IT>>
Help Your Clients Keep Their Systems, Data and Patients Safe
Now is the ideal time to connect with your healthcare sector clients and make sure that they’ve got strong security in place to help them stay out of trouble. Our security solutions give you the tools that you need to protect their systems, data and patients from dangerous cyberattacks affordably.
Security awareness and compliance training plus phishing simulation
BullPhish ID is the ideal security and compliance awareness training solution for companies of any size.
- An extensive library of security and compliance training videos in eight languages
- Plug-and-play or customizable phishing training campaign kits
- New videos arrive 4x per month and new phishing kits are added regularly
- Easy, automated training delivery through a personalized user portal
Dark web monitoring
Dark Web ID offers best-in-class dark web intelligence, reducing credential compromise risk.
- 24/7/365 monitoring using real-time, machine and analyst-validated data
- Fast alerts of compromises of business and personal credentials, including domains, IP addresses and email addresses
- Live dark web searches find compromised credentials in seconds
- Create clear and visually engaging risk reports
Automated, AI-powered antiphishing email security
Graphus AI-enabled, automated email security that catches 99.9% of sophisticated phishing threats and offers amazing benefits.
- Forget old-fashioned safe sender lists. Graphus analyzes the content of messages using more than 50 points of comparison to suss out fakes fast.
- Cloud-native security harnesses machine learning to inform AI using a patented algorithm.
- 3 layers of powerful protection at half the cost of competing solutions
- Don’t waste time on fussy configurations or adding threat reports. AI does that for you, getting everything up and running with just a few clicks and minimal maintenance.
Click here to watch a video demo of Graphus now.
NEW INTEGRATION! If you’re already using BullPhish ID for security and compliance awareness training and phishing simulations, you’ll love our latest integration Advanced Phishing Simulations (Drop-A-Phish). This feature leverages the power of integration with Graphus to eliminate the need for domain whitelisting and ensure 100% campaign deliverability to end users when running phishing simulations. LEARN MORE>>

Make sure your clients have all the bases covered with the Computer Security To-Do Checklist! GET IT>>


August 23: How to Grow Your Revenue with Dark Web ID REGISTER NOW>>
August 25: A 15-Minute Demo: Graphus AI-Driven Email Security REGISTER NOW>>
August 30: Robin Robins Roadshow Philadelphia REGISTER NOW>>
September 16: Cybersecurity Summitt in Charlotte REGISTER NOW>>

Read case studies of MSPs and businesses that have conquered challenges using Kaseya’s Security Suite. SEE CASE STUDIES>>

Do you have comments? Requests? News tips? Complaints (or compliments)? We love to hear from our readers! Send a message to the editor.
ID Agent Partners: Feel free to reuse this content. When you get a chance, email [email protected] to let us know how our content works for you!