The Ink This Week: Cybersecurity and Threat News 09/11/20

Go Inside the Ink to See What’s New in Cybersecurity News This Week
NEW CYBERSECURITY NEWS: MUST-READ BLOGS
We publish new posts every weekday featuring cybersecurity and threat news, insight, analysis, and solutions to help you prepare for the threats of tomorrow. BOOKMARK IT>>
SEPTEMBER BLOG FEATURES
It’s National Preparedness Month. While you’re updating your Home Disaster Preparedness Plan, you should update your Cybersecurity Disaster Preparedness Plan too. Every Thursday, we’ll be featuring advice and tips for preparing for cybersecurity disasters, including business continuity, cybersecurity incident response, the anatomy of a data breach, and lessons learned from the COVID-19 pandemic to give you the information that you need to update your Cybersecurity Disaster Plan for 2021.
Get to Know Graphus. The newest addition to our digital risk protection platform is Graphus, an innovative automated phishing defense solution. Graphus uses patented smart AI technology with an algorithm that evolves with your business to put 3 layers of protection between a phishing email and an employee inbox. We’ll show you how Graphus can give you peace of mind against phishing (today’s biggest threat) every Tuesday.
NEW CYBERSECURITY NEWS: SEE THE THREAT OF THE WEEK & HOW TO STOP IT
These Days, Data Breach Risks Come From Unexpected Sources
As We Provide More Personally Identifying Information to More Places, the Risk of That Information Being Stolen is Higher, and That’s Bad for Your Business
We’ve learned to consider the possibility of information and data theft at companies that we deal with for business like merchants, service providers, and suppliers. We’re aware of how our personal information can be stolen and used for cybercrime from common sources in our personal lives, like credit card companies, hospitals, or retailers. But what we’re often not considering is small but impactful ways that cybercriminals can get our PII and other sensitive data and use it for cybercrime against us.
Every day, we log into dozens of applications at work and at home – some we don’t even think about. Automated assistants, IoT devices, entertainment platforms, schedulers: we’re all using more apps and more technology than ever – and every one of those things wants at least some of our personal information. Many also require us to give a username, password, and email address. But remembering each one can be challenging, so people often use unsafe password handling habits, creating sources of risk.
We also have to provide our personal information to complete many routine tasks, like refilling a prescription, going to the gym, or using a frequent shopper card. These are the kind of PII uses that open you up to third party risks that you may not have considered – and that can create real problems as we move into an even more automated, online society.
For example, thieves used recent civil unrest in the US as a cover to break into several Walgreens stores and steal prescription information and other data on some 70,000 customers. The thieves stole hard drives that contained customers’ health insurance, prescription, condition, allergy, contact, history, consultation, treatment, and vaccination information as well as PII.
This data is useful to cybercriminals in several ways:
- Spear Phishing for Credentials: You might not fall for an email asking you to provide login information for a system at work, but you’d probably be much less suspicious of an email from your doctor’s office asking you to “log in and confirm your information in their new system.”
- Blackmail: Are you being treated for something that you don’t want people to know about? Is a member of your staff? Threats of exposure can lead staffers to pay bribes or give up information that they normally wouldn’t, like login credentials for a business account.
- Identity Theft: Criminals that have your PII and some details about your life can use that data to obtain more details and steal your identity to perpetrate fraud, like convincing a service provider that they’re you in order to obtain credentials that enable them to access your company’s data and systems.
So, how can you prevent this from becoming a problem for your business?
THE THREAT
STOP IT
Quickly put the brakes on anyone attempting to steamroll their way into your company’s data and systems through phishing, fraud, or password compromise by adding a secure identity and access management solution like Passly. Here’s how it protects your business from this kind of threat.
- Multifactor authentication makes stolen passwords useless because the password thief needs a second identifier, like a code given through an app on the user’s phone, to gain access to your protected data and systems.
- Single sign-on protects your business by creating individual Launchpads for each user that form their point of access to applications, equipment, and data. If a user’s login credentials are compromised, you only need to disable their launchpad instead of adjusting individual permissions in each program they use.
- Password reuse is no longer a problem because every user’s login to their personalized Launchpad is unique and requires authentication, so even if cybercriminals do get passwords to your systems or gather enough ammunition to try and get lucky with a credential stuffing attack, Passly’s security tools will stop them.
SEE A DEMO VIDEO OF PASSLY NOW>>>
NEW RESOURCES

What Threats Should Be on Your Watch List? See How Cybercrime Has Changed in 2020 and Where We Think Cybercrime is Headed in 2021.
2020 has been a year of massive change for everyone in every industry. The global pandemic, economic challenges, civil unrest, natural disasters, and a general feeling of unease have created an atmosphere that allows cybercrime to flourish. In order to get a grip on the biggest threats to your information and systems, you need a clear picture of what really happened in cybersecurity in 2020, and what you can expect to be a threat to your business in 2021 – and we’re here to help.
Phishing has been the biggest, boldest, baddest threat of 2020. With a more than 600% increase in phishing email and many new styles of phishing attack in play, protecting your business from phishing has to be your top cybersecurity priority in 2021. Our analysis of danger from phishing threats like ransomware in 2020 is here, and ready to help you defend your business from today’s nastiest threats..
The Dark Web has grown exponentially in size and danger in 2020. In a challenging economy, even cybercriminals have to work a little bit harder, and they’ve already started developing and launching audacious attacks that will create new dangers for businesses in the future. Between the flood of information on the Dark Web from past data breaches and the rise of cybercrime as a service, understanding how the evolution of the Dark Web economy drives cybercrime.
IN CASE YOU MISSED IT LAST WEEK MSPs: Go behind the scenes and see what really happens on the Dark Web with experts to give you all of the information that you need to protect your business and your clients in an MSP-focused webinar >>
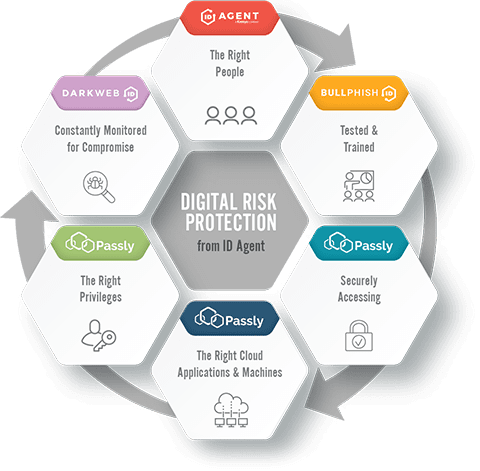
ID AGENT’s Digital Risk Protection Platform and Security Awareness Training empowers every business to fight back against Dark Web threats!
Get an expert analysis of your risk including a FREE Dark Web Report using the power of DARK WEB ID
Join forces with us to gain access to our industry-leading sales and marketing support – we’ll even join you on tough sales calls!