The Week in Breach News: 08/24/22 – 08/30/22

It’s all ransomware all the time this week with a spate of damaging attacks in the U.S., U.K. and South America. Plus, find out which training videos are the most popular and take a look at the two threats that make up almost three-quarters of cyberattacks. A convoluted BEC scam rocks a Pennsylvania school district, more fallout from the Twilio hack plus a look at rising supply chain risk and what you can do to protect yourself and your clients.

Find the perfect training solution for your clients & your MSP with our MSP-focused buyer’s guide. DOWNLOAD IT>>

Accelya
https://therecord.media/major-airline-technology-provider-accelya-attacked-by-ransomware-group/
Exploit: Ransomware
Accelya: Airline Technology Services

Risk to Business: 1.706 = Severe
The AlphV/Black Cat ransomware group has claimed responsibility for an attack on airline technology firm Accelya. The group claimed to have stolen emails, worker contracts and other business information. Accelya provides passenger, cargo, and industry analytics platforms for airline retailing to Delta, British Airways, JetBlue, United, Virgin Atlantic, American Airlines and other airlines. The company confirmed the incident after investigators discovered that the company’s data was posted on a ransomware leak site.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How It Could Affect Your Customers’ Business: This company faced double jeopardy with both an increase in supply chain and transportation industry attacks.
ID Agent to the Rescue: Gain 3 resources featuring a wealth of knowledge about ransomware and how to keep your clients safe from our Introduction to Ransomware Resource Bundle! DOWNLOAD THE BUNDLE
DoorDash
Exploit: Supply Chain Attack
DoorDash: Food Delivery Service

Risk to Business: 1.907 = Severe
DoorDash has confirmed a data breach that has exposed customer information. Employees of the vendor had credentials that were stolen as part of a recent incident at software company Twilio that were then used to access DoorDash’s internal tools. The company said it cut off the third-party vendor’s access to its systems after discovering suspicious activity. DoorDash did not name the third-party vendor but did confirm the attack and that it was related to the Twilio hack.

Individual Risk: 1.975 = Severe
An undisclosed number of customers had their names, email addresses, delivery addresses, phone numbers and partial payment card numbers stolen. For drivers with the company, hackers were able to access names, phone numbers and email address information.
How It Could Affect Your Customers’ Business: Unfortunately, this kind of exposure is becoming all too common as bad actors strike strategically against service providers.
ID Agent to the Rescue: Our Monsters of Cybersecurity eBook helps you discover and mitigate the killer risks that are lurking around every corner. DOWNLOAD IT>>
LastPass
https://www.theregister.com/2022/08/25/lastpass_security/
Exploit: Ransomware
LastPass: Software Company

Risk to Business: 1.836 = Severe
Authentication software firm LastPass said on Thursday that someone broke into one of its developer’s accounts and used that to gain access to proprietary data including source code. The company said in a statement that the incident had been contained and that they see no further evidence of unauthorized activity. LastPass says there is no evidence that customer data or encrypted password vaults were compromised. This breach may be related to the recent Twilio hack which impacted many companies.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How It Could Affect Your Customers’ Business: The Information Technology sector was one of the 14 critical infrastructure sectors most victimized by ransomware last year.
ID Agent to the Rescue: See the biggest risks that businesses in different sectors face today and get a look your clients will be facing tomorrow in The Global Year in Breach 2022. DOWNLOAD IT>>
Chester Upland School District
Exploit: Business Email Compromise
Chester Upland School District: Regional Education Authority

Risk to Business: 1.337 = Severe
A recent business email compromise attack on a Pennsylvania school district resulted in bad actors making off with more than $13 million. Authorities say hackers used a stolen district employee email account to snatch the money by sending official-looking messages from that account and then diverting payments to themselves. After diverting the payments, the cybercriminals then used a romance scam conducted through the dating site eHarmony to entice a Florida woman to launder the money unwittingly. The scheme came to light after the Pennsylvania Department of the Treasury flagged a large transfer, unraveling the whole mess. $10 million of the money has since been recovered.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business: Business email compromise is hard to detect but causes the most financial damage. This school district got lucky recovering money.
ID Agent to the Rescue: Learn to build an effective program that reduces cyberattack risk with the guide How to Build a Security Awareness Training Program. DOWNLOAD IT>>
New Hampshire Lottery
https://www.wmur.com/article/new-hampshire-lottery-website-experiences-cyber-attack/41000488
Exploit: Hacking
New Hampshire Lottery: Gambling Program

Risk to Business: 2.809 = Moderate
New Hampshire Lottery officials warned of a cyberattack on its website, cautioning players that people visiting the site should not click on any pop-up message. The site began to experience trouble early Friday morning, typically a busy day for lottery sales with the Mega Millions drawing taking place late Friday night. Officials said the site has been taken down as the matter is investigated and the trouble dealt with. They do not believe any personal data of players was stolen.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business: Cybercriminals love to exploit government-run websites to spread malware or for other nefarious purposes.
ID Agent to the Rescue: Are you offering the right training solution to help your clients avoid risks like this? Find out with the Security Awareness Training: Buyer’s Guide for MSPs DOWNLOAD IT>>

See five things that you can do to reduce nation-state cyber threat risk for your clients fast. GET CHECKLIST>>
The Dominican Republic – Instituto Agrario Dominicano
Exploit: Ransomware
The Instituto Agrario Dominicano (IAD): Government Agency

Risk to Business: 1.223 = Severe
The Instituto Agrario Dominicano (IAD), an arm of the Dominican Republic’s Ministry of Agriculture, has been hit by the Quantum ransomware group. The attack took down four physical and eight virtual servers as well as compromising all of IAD’s data. Officials say that the agency had only basic security in place and no dedicated security workers. The group is demanding an estimated $600k in ransom, but The Dominican Republic is an economically challenged country, making it unlikely that they’ll pay the extortionists.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business: Governments have been popular targets for cybercriminals even when they’re not nation-state aligned.
ID Agent to the Rescue: See the reasons why an AI-driven automated email security solution is the answer to email security challenges and why you and your clients will love it. DOWNLOAD INFOGRAPHIC>>

Learn to identify and mitigate fast-growing supply chain risk with this eBook. DOWNLOAD IT>>

Greece – DESFA
https://therecord.media/greek-gas-operator-refuses-to-negotiate-with-ransomware-group-after-attack/
Exploit: Ransomware
DESFA: National Natural Gas Provider

Risk to Business: 2.871 = Moderate
Greece’s national natural gas operator DESFA has been hit by a ransomware attack by the Ragnar Locker ransomware organization. The group added DESFA to its dark web leak site on Friday, noting that it had not received a response to its ransom demand at that time. DESFA said that it will not negotiate with cybercriminals. The company also said that the incident had a “confirmed impact on the availability of some systems and possible leakage of a number of directories and files.” DESFA also said that Greek law enforcement agencies as well as the Ministry of Digital Governance and Hellenic Data Protection Authority have been notified of the attack.
Individual Impact: No information about consumer/employee PII, PHI or financial data exposure was available at press time.
How it Could Affect Your Customers’ Business: Cybercriminals love to go after utilities because of the high chance they’ll get paid to avoid service disruptions, although these bad actors won’t.
ID Agent to the Rescue: Learn more about the business of ransomware including how the bad guys get paid and get tips for securing your clients in Ransomware Exposed! DOWNLOAD EBOOK>>

Insider risk is up by 40%. Help your clients stay out of trouble with The Guide to Reducing Insider Risk GET IT>>

India – Akasa Air
Exploit: Misconfiguration
Akasa Air: Airline

Risk to Business: 1.790 = Severe
Akasa Air disclosed that it has suffered a data breach resulting in unauthorized individuals gaining access to user information. The breach was caused by a configuration error that left vulnerabilities in the airline’s login and sign-up service. Akasa Air said that no travel-related information, travel records or payment information was compromised in the incident. The company claims to have fixed the problem and reopened all services.

Risk to Business: 1.662 = Severe
Exposed registered user information includes registrant names, genders, email addresses and phone numbers.
How it Could Affect Your Customers’ Business: Employee mistakes like this one can be just as costly and problematic as a cyberattack.
ID Agent to the Rescue: Gain insight into identifying and mitigating both accidental and malicious insider risk for your clients in The Guide to Reducing Insider Risk. DOWNLOAD IT>>

See cybercrime trends & the results of thousands of phishing simulations in The Global Year in Breach 2022. DOWNLOAD IT>>

1 – 1.5 = Extreme Risk
1.51 – 2.49 = Severe Risk
2.5 – 3 = Moderate Risk
Risk scores for The Week in Breach are calculated using a formula that considers a range of factors for each incident

See how today’s biggest threats may impact your MSP and your customers in our security blogs.
- Ransomware Attacks on Healthcare Organizations Have Devastating Results for Providers & Patients
- Almost Three-Quarters of Cyberattacks Have Something in Common: Phishing
- Why You Should Be on the Lookout for Spear Phishing & How to Spot It
- 4 Reasons Why Ransomware Risk Won’t Stop Rising for SMBs
- The Week in Breach News: 08/17/22 – 08/23/22

Passly Introduces Enhanced Protection for User Accounts via Dark Web ID Integration
Passly will help IT admins ensure their users act faster to change their passwords in the event they’ve been compromised — before damage is done.
How it works:
- The integration with Dark Web ID* creates real-time notifications any time a Passly user has their account exposed on the dark web.
- Passly will alert IT admins to the activity and, optionally, trigger a password change.
- This capability is enabled automatically when Dark Web ID and Passly are used together. No configuration is required.
For more details about this feature and other release notes for Passly, check out this article.
*You have to subscribe to both Passly and Dark Web ID to take advantage of this integration.

Solve five of the most exhausting remote and hybrid security problems fast with this handy infographic! DOWNLOAD IT>>

Grow Your Security & Compliance Training Business
It’s time to get employees back to class for security and compliance education. These resources will help you start or continue profitable conversations with your clients and prospects about the importance of training!
Security Awareness Training: Buyer’s Guide for MSPs – Learn about security awareness training solutions plus how to find the right one for your MSP and your customers. DOWNLOAD IT>>
BullPhish ID: The Leader in Security Awareness Training – Get to know the features and benefits that make BullPhish ID a leader in the security awareness and phishing resistance training space! WATCH NOW>>
The Business Case for Security Awareness Training – Give this resource to your customers to make the case that security and compliance training is a winning investment with great results and high ROI. DOWNLOAD IT>>
Did you miss… The Building a Strong Security Culture Checklist? DOWNLOAD IT>>

Go inside nation-state cybercrime to get the facts and learn to keep organizations safe from trouble! GET EBOOK>>


Software Supply Chain Risk is a Major Concern for Businesses
Learn More to Protect Your MSP & Your Clients
Software supply chain risk has been an ongoing battle for businesses that is fast becoming a top concern for CISOs. Cybercriminals have been making adjustments to choose strategic targets like infrastructure and key linchpins in the service and supply chain, especially in the technology sector. IBM predicted that supply chain cyberattacks would be a major concern for businesses in 2022, and they were on target. Business leaders are becoming more aware of supply chain risk in general as well as risk in the software supply chain that could harm their organizations, and they’ll be looking to MSPs and other IT professionals to help them navigate and mitigate that risk.

Find the right dark web monitoring solution for your customers & your MSP with this checklist! DOWNLOAD IT>>
Why is software supply chain risk escalating?
Software supply chain risk is growing, and a host of factors have gone into brewing up today’s stormy risk landscape. In a time of increased scrutiny and legal action toward cybercrime, many cybercriminal gangs are taking the time to choose strategic targets, especially in the case of high-end or state-sponsored ransomware groups. They’re concentrating fire on targets that can give them a quick payoff, like stores of valuable data, or increase their ability to conduct future attacks, like finding ways to penetrate security at other businesses through back doors.
Adding to the mix, many service providers and suppliers like software and technology companies are in critical infrastructure sectors and cannot afford downtime, making them highly likely to pay. Attacks on critical infrastructure targets have been escalating in recent years, with 14 of 16 critical infrastructure sectors experiencing ransomware attacks in 2021, including technology companies. U.S. Federal Bureau of Investigation Internet Crime Complaint Center (FBI IC3), listed the most endangered critical infrastructure and supply chain targets for 2021 in its most recent report. The information technology center came in third place with 74 ransomware attacks, behind first-place finisher Healthcare & Public Health at a whopping 148 ransomware attacks and runner-up Financial Services at 89 ransomware attacks.
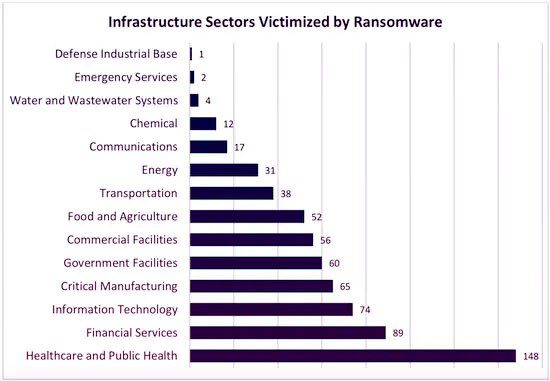
Source: FBI IC3

Learn to unleash the power of checklists and other downloads in your marketing efforts! WATCH WEBINAR>>
MSPS are targets in the software supply chain
MSPs have not escaped the cybercriminal grasp. MSSP Report noted that an estimated 90% of MSPs said in a survey that they’ve suffered a successful cyberattack in the last 18 months. Those attacks have brought a number of complications in their wake that keeps the pain coming for affected MSPs. More than 50% of MSPs say that they experienced significant financial loss and business disruption after a cyberattack. The rising tide of attacks on MSPs is also driving them to spend more on security at a time when economic challenges mean that every penny counts. Four out of five MSPs in a recent survey said that they’re increasing their security budgets to contend with elevated risk.
Attacks on MSPs can bring cybercriminals many benefits by offering them a wealth of tools, options and opportunities that they can exploit for further gain. MSPs tend to store and handle valuable information, including customer data and information about operational technology (OT). Attacks on MSPs also offer the bad guys chances to obtain access to the MSPs customers’ environments, allowing them to quickly penetrate security at another company that they’ve been trying to go after. A successful attack at an MSP can even offer cybercriminals the advantage that they need to plant a backdoor in that MSPs client’s environment, enabling the bad guys to return at their leisure for further dirty work.

Get tips from experts in our webinar MSP Cybersecurity Roundtable: How to Improve Your Incident Response Plan WATCH NOW>>
Business leaders are growing increasingly more concerned about software supply chain risk
Overall, IT professionals and business executives are worried about the risk they may inherit from their software supply chain, and those worries are well founded. More than 80% of CISOs told Forbes that they believe that their software supply chains are vulnerable and could bring trouble to their organizations. Corporate IT professionals who are in the trenches every day are also concerned. More than half of IT managers in a survey said that they’re concerned that their software supply chain exposes their company to an attack. While some of that risk can be mitigated through training and defensive enhancements, some of it is simply out of their hands, upping their stress levels.
Unfortunately, more often than not they’re right to worry. The software supply chain has been getting hammered, with an estimated three out of five businesses saying in a survey that they have been targeted in a software supply chain attack. Business relationships are also concerning for IT professionals and business leaders, especially from service providers. Most CISOs are worried about vulnerabilities and risk exposure coming into their sphere from their organization’s business relationships. Forbes magazine reports that about 44% of CISOs and executives fear that their growing use of partners and suppliers exposes their organizations to major security risks. All in all, 54% of respondents pegged supply chain risk as a top area of focus for security anxiety.

Get 10 tips to help you build a strong security culture & reduce your risk of cybersecurity trouble! GET INFOGRAPHIC>>
3 NIST tips for reducing software supply chain risk
The U.S. National Institute for Standards and Technology (NIST) has made several recommendations for reducing software supply chain danger that MSPs can employ to reduce risk for their customers and themselves.
Automation makes a difference
The NIST guidance for reducing software supply chain risk includes a push toward security automation for businesses. Some of the guidance can’t be followed without it. Automation and AI are powerful tools that reduce risk quickly.
Ensure that every employee is doing their part
Every worker in an organization must be aware of their responsibility to help preserve security. Addressing vulnerabilities like a lack of training, a weak security culture or sloppy security practices keeps a worker’s company safe and helps secure business partners too.
Prioritization is a key component of supply chain risk management.
Developing a formal understanding of where the greatest risk lies in a company’s supply chain and how to prioritize the risks a company faces are critical moves to make for reducing exposure to software supply chain risk and strengthening that company’s defenses.

Learn the secret to conjuring up amazing stress-free marketing campaigns in 5 Ways to Make Marketing Magic! GET IT>>
Help your clients reinforce their defensive posture to reduce cyberattack risk
Reducing your clients’ risk of a cyberattack is an ongoing battle, but these solutions can help ensure that you’re using the best weapons to fight back against cybercrime and putting safeguards in place that are ready to handle the next generation of cyber threats.
Security awareness and compliance training plus phishing simulation
BullPhish ID is the ideal security and compliance awareness training solution for companies of any size.
- An extensive library of security and compliance training videos in eight languages
- Plug-and-play or customizable phishing training campaign kits
- New videos arrive 4x per month and new phishing kits are added regularly
- Easy, automated training delivery through a personalized user portal
Dark web monitoring
Dark Web ID offers best-in-class dark web intelligence, reducing credential compromise risk.
- 24/7/365 monitoring using real-time, machine and analyst-validated data
- Fast alerts of compromises of business and personal credentials, including domains, IP addresses and email addresses
- Live dark web searches find compromised credentials in seconds
- Create clear and visually engaging risk reports
Automated, AI-powered antiphishing email security
Graphus AI-enabled, automated email security that catches 99.9% of sophisticated phishing threats and offers amazing benefits.
- Forget old-fashioned safe sender lists. Graphus analyzes the content of messages using more than 50 points of comparison to suss out fakes fast.
- Cloud-native security harnesses machine learning to inform AI using a patented algorithm.
- 3 layers of powerful protection at half the cost of competing solutions
- Don’t waste time on fussy configurations or adding threat reports. AI does that for you, getting everything up and running with just a few clicks and minimal maintenance.
Click here to watch a video demo of Graphus now.
NEW INTEGRATION! If you’re already using BullPhish ID for security and compliance awareness training and phishing simulations, you’ll love our latest integration Advanced Phishing Simulations (Drop-A-Phish). This feature leverages the power of integration with Graphus to eliminate the need for domain whitelisting and ensure 100% campaign deliverability to end users when running phishing simulations. LEARN MORE>>

Make sure your clients have all the bases covered with the Computer Security To-Do Checklist! GET IT>>

September 6: Clobber Phishing Risk with a BullPhish ID Dynamic Duo REGISTER NOW>>
September 11-13: DattoCon REGISTER NOW>>
September 16: Cybersecurity Summitt in Charlotte REGISTER NOW>>
September 28-30: SpiceWorld 2022 REGISTER NOW>>
October 6-7: ASCII MSP Success Summit 2022 – Dallas REGISTER NOW>>
October 13: Cybersecurity Summit in Scottsdale REGISTER NOW>>
October 25-26: Southwest US Summit REGISTER NOW>>
November 2-3: ChannelPro SMB Forum 2022: Los Angeles REGISTER NOW>>
December 6: Connect IT Local – Atlanta REGISTER NOW>>
December 8: Connect IT Local – Miami REGISTER NOW>>

Read case studies of MSPs and businesses that have conquered challenges using Kaseya’s Security Suite. SEE CASE STUDIES>>

Do you have comments? Requests? News tips? Complaints (or compliments)? We love to hear from our readers! Send a message to the editor.
ID Agent Partners: Feel free to reuse this content. When you get a chance, email [email protected] to let us know how our content works for you!