The Week in Breach: Cybersecurity and Breach News 08/05/20 – 08/11/20
This Week in Cybersecurity & Breach News: Ransomware hits everywhere from small towns to multinational corporations and tech giants, how to add protection against nation state actors, a new FBI warning about ransomware targeting US companies, and new webinars with marketing tools and product-based strategies to grow your MRR.
Cybersecurity News: Dark Web ID’s Top Threats
- Top Source Hits: ID Theft Forum
- Top Compromise Type: Domain
- Top Industry: Education & Research
- Top Employee Count: 501+
Cybersecurity and Breach News – United States
United States – UberEats
Exploit: Unauthorized Database Access
Uber Eats: App-Based Food Delivery Service

Risk to Small Business: 2.691 = Moderate
Security analysts doing routine Dark Web and Deep Web monitoring uncovered a data dump containing details about customers, delivery drivers, and delivery partners for UberEats. The 9 TXT files leaked by the threat actor include login credentials of 579 UberEATS customers and details of 100 delivery drivers. The data includes login credentials, full name, contact number, trip details, bank card details, and, account creation dates.

Individual Risk: 2.377 = Severe
No details about how affected customers and drivers will be informed or any remediationn offered have been released. UberEats customers, drivers, and partners should reset their account credentials and be alert for credit card fraud, spear phishing, and identity theft dangers.
Customers Impacted: 679
How it Could Affect Your Customers’ Business: This breach is especially troubling because it is unacknowledged and it was discovered by Dark Web analysts instead of internal IT, putting in question the company’s transparency about security and attention to small security issues.
ID Agent to the Rescue: This breach was detected by experts doing Dark Web analysis. Put the power of Dark Web ID to work for your clients detecting and alerting when compromised credentials are discovered LEARN MORE>>
United States – Summit Medical Associates
Exploit: Ransomware
Summit Medical Associates: Healthcare Provider

Risk to Small Business: 1.979 = Severe
A data breach has come to light at Summit Health after the Tennessee-based practice group reported that it had experienced an “inability to access certain records” in early June. A tired arty investigator determined that not only was it a ransomware incident, but the cybercriminals had also been able to access to their systems for nearly six months before the breach.

Individual Risk: 2.799 = Moderate
There has been no reported no evidence that patient information was compromised, the affected server did contain patient PII including names, medical information, and Social Security numbers.
Customers Impacted: Unknown
How it Could Affect Your Customers’ Business Cybercriminals had access to this server for six months before anyone noticed. Security awareness, data handling, credential monitoring, and phishing resistance training keep eyes on the ball for cybersecurity, lowering the chance that something like this happens (or persists).
ID Agent to the Rescue: The security awareness and phishing resistance training that forms part of our digital risk protection platform helps stop negligence like this from starting. LEARN MORE>>
United States – The Blacklist Alliance
https://krebsonsecurity.com/2020/08/robocall-legal-advocate-leaks-customer-data/?web_view=true
Exploit: Unauthorized Database Access
The Blacklist Alliance: Robocall Legal Advocate

Risk to Small Business: 1.717 = Severe
In an ironic turn of events, The Blacklist Alliance, a company that helps telemarketers dodge lawsuits from violations of the Telephone Consumer Protection Act, has experienced a data breach that leaked the phone numbers, email addresses and passwords of all its customers, as well as mobile phone numbers and data on people who have hired lawyers to go after telemarketers. Thousands of documents, emails, spreadsheets, images, and the names tied to a huge number of mobile phone numbers were freely accessible from the domain theblacklist.click. The directory also included all 388 Blacklist customer API keys, as well as each customer’s phone number, employer, username, and password ( hashed using the MD5 algorithm).

Individual Risk: 1.912 = Severe
Individuals and companies who have done business with The Blacklist Alliance should consider their information at risk for fraud, identity theft, blackmail, or spear phishing attempts.
Customers Impacted: 388+
How it Could Affect Your Customers’ Business: A failure to secure PII and other sensitive data in an industry that handles secretive personal matters like this can be disastrous. Not only does it open the company up to legal and reputational risk, but it also risks the company’s ability to keep doing business in an industry that prizes anonymity.
ID Agent to the Rescue: Secure access points to delicate information by adding Single Sign-on with Passly. By assigning each user an individual launchpad, you’re able to control access to sensitive data more carefully – and act faster if the wrong person gets access. SEE A DEMO>>
United States – CWT
Exploit: Ransomware
CWT: Travel Management

Risk to Small Business: 1.882 = Severe
CWT reportedly paid an eye-popping $4.5 million to cybercriminals using Ragnar Locker ransomware to decrypt reams of sensitive corporate files and restore 30,000 company computers that were knocked offline. Reportedly, the hackers initially demanded $10 million. Reuters included details and screenshots of the negotiation in a story filed last week. The ransom note left by the hackers claimed to have stolen two terabytes of files, including financial reports, security documents, and employees’ personal data such as email addresses and salary information.
Individual Risk: No personally identifiable information or financial information was reported as stolen/
Customers Impacted: Unknown
How it Could Affect Your Customers’ Business: The most common delivery system for ransomware is a phishing email – and 90% of incidents that end in a data breach start with a phishing email. Boosting phishing resistance is essential to lower the chance of a successful ransomware attack.
ID Agent to the Rescue: BullPhish ID offers training in 8 languages to get staffers up to speed on today’s phishing threats fast, including video lessons and online testing. Learn more>>
United States – Boyce Technologies
Exploit: Ransomware
Boyce Technologies: Medical Equipment Manufacturer

Risk to Small Business: 1.407 = Extreme
Essential medical equipment producer Boyce Technologies was attacked with DoppelPaymer ransomware. The company produces about 300 low-cost ventilators per day using human and robotic labor. Microsoft noted that this type of ransomware uses “brute force” against a target company’s systems management server. It has extensively targeted the healthcare sector since the start of the COVID-19 crisis.
Individual Risk: No personal or financial information was reported as compromised.
Customers Impacted: Unknown
How it Could Affect Your Customers’ Business: Ransomware attacks have grown more sophisticated and more dangerous in 2020, and corporate-level espionage that impacts production has become more prevalent – meaning that companies have to be more cautious about closing security loopholes.
ID Agent to the Rescue: In a challenging economy, it can be difficult to convince customers that they need to increase security to avoid these potentially devastating attacks. That’s why our Partners love the extra help that they can call on through Goal Assist to help seal a tricky deal. Learn More >>
United States – City of Lafayette, Colorado
https://www.securityweek.com/colorado-city-pays-45000-ransom-after-cyber-attack?&web_view=true
Exploit: Ransomware
City of Lafayette, CO: Municipal Government

Risk to Small Business: 2.101 = Severe
The City of Lafayette, CO paid $45k to cybercriminals to restore access to municipal computers after a successful ransomware attack shut municipal networks down including city emails, phones, online payments, and reservation systems. The cost of restoration and the impact of the shutdown on city services impacted the city’s calculations when choosing to pay the ransom or restore from backups.

Individual Risk: 2.801 = Moderate
City officials say that credit card information was not compromised, and there was no evidence that personal data was stolen either, residents should monitor their accounts for suspicious activity as a precaution.
Customers Impacted: Unknown
How it Could Affect Your Customers’ Business: Ransomware can be so damaging that paying the ransom is less than the cost of recovery. Without adequate protections in place including updates security awareness training and access controls, organizations (and their budgets) can take a big hit from ransomware.
ID Agent to the Rescue: Over 3,000 MSPs in 30 countries trust our solutions to help protect their customers from threats like ransomware. Our new Partners typically realize ROI in 30 days or less, and we’ve always got room for more. Contact us to learn more about the benefits of Partnership. Learn more>>
Cybersecurity and Breach News – Canada
Canada – Nova Scotia Health Authority
Exploit: Unauthorized Database Access
Nova Scotia Health Authority: Healthcare System

Risk to Small Business: 2.662 = Moderate
Not one but two security breaches at the Nova Scotia Health Authority have been reported as patient data was accessed by unauthorized individuals. The information was reported as “viewed”, but no details were given on how or by whom. The Nova Scotia Health Authority said it had notified the province’s Office of the Information and Privacy Commissioner.

Individual Risk: 2.874 = Moderate
The Authority said that it has notified the small number of patients affected, and did nor report ant financial information as stolen in either incident.
Customers Impacted: 211
How it Could Affect Your Customers’ Business: Sensitive information, especially medical data, requires an extra level of care for protection – or the company that mishandles it will find themselves paying large fines in addition to other remediation costs.
ID Agent to the Rescue: Passly secures sensitive data with multifactor authentication, ensuring that a second form of identification is required for anyone to access protected systems and data. Learn more>>
Cybersecurity and Breach News – United Kingdom & European Union
United Kingdom – British Dental Association
https://www.bbc.com/news/technology-53652254?&web_view=true
Exploit: Unauthorized Database Access
British Dental Association: Trade Union

Risk to Small Business: 1.866 = Severe
The British Dental Association informed its members that data on a “small fraction” of its membership was exfiltrated in late July. The statement was vague about the cause or impact, and the organization’s website has been down since the attack was reported on 7/30/20. The association is still working to restore its web, telephone, and internal networks following the security breach, and has notified the Information Commissioner’s Office.

Individual Risk: 2.219 = Severe
The organization does not store members’ card details but does hold account numbers and sort codes to collect direct debit payments. The BDA has urged its members to remain vigilant against identity theft or spear phishing attempts.
Customers Impacted: 22,000
How it Could Affect Your Customers’ Business: When an organization stores the financial information of its members in any capacity, that information needs to be protected – and members need to have confidence in the security of their personal and financial data on file, especially in professional groups or trade unions.
ID Agent to the Rescue: Passly’s cutting-edge features make it the best cost-effective secure identity and access management solution to add to your security stack to guard against unwelcome visitors to your clients’ systems and data. SEE PASSLY’S FEATURES >>
France – Forsee Power
Exploit: Ransomware
Forsee Power: Electromobility Battery Manufacturer

Risk to Small Business: 1.113 = Severe
Netwalker ransomware is to blame for the leak of extensive business data at the Paris-based battery manufacturer, a world leader in electric mobility device power. Cybercriminals exposed a directory containing folders such as Accounts Receivable, Finance, Collection Letters, Expenses, and Employees in an image posted to the Netwalker group blog.
Individual Risk: No personal or financial information was reported as stolen in this incident.
Customers Impacted: Unknown
How it Could Affect Your Customers’ Business: Sensitive business data is valuable – and it sells for a pretty penny on the Dark Web. Smart companies use Dark Web monitoring to stay on guard against the exposure of sensitive credentials and information on the Dark Web.
ID Agent to the Rescue: Today’s Dark Web is a very different place than it was before COVID-19. Don’t overlook the danger to your clients and your MSP that is ramping up from the thriving Dark Web data markets. Go inside these markets with experts to see the real Dark Web in our newest webinar, featuring an MSP perspective and real Dark Web screenshots. Get the Webinar>>
Cybersecurity and Breach News – Asia
Japan – Canon
https://www.bleepingcomputer.com/news/security/canon-confirms-ransomware-attack-in-internal-memo/
Exploit: Ransomware
Canon: Optical and Imaging Products Manufacturer

Risk to Small Business: 2.231 = Severe
International equipment behemoth Canon reported in a letter to staffers that it had been the victim of a ransomware attack that Canon impacted numerous services, including Canon’s internal email, Microsoft Teams, USA website, and other essential business applications. The Maze ransomware group has claimed credit for the successful attack and disruption of Canon’s business systems. Maze operators stated that they extracted 10 terabytes of data on private databases in the attack. Canon notes that some users’ still image and video image data stored in its image.canon cloud photo platform involving the 10GB long-term storage option was missing but offered no details as to the type of images that were taken.
Individual Risk: At this time, there is no available information about the nature or provenance of the stolen data.
Customers Impacted: Unknown
How it Could Affect Your Customers’ Business: Maze ransomware attacks typically start with gaining access to an average employee account and using that to gain access to accounts with greater privilege – and the vast majority of ransomware attacks start off as phishing.
ID Agent to the Rescue: Strengthen phishing resistance at every level with BullPhish ID. Easy management and deployment tools make it simple to create customized groups of users for testing. Learn more>>
Cybersecurity and Breach News – Australia & New Zealand
Australia – ProctorU
Exploit: Unauthorized Database Access
ProctorU: Online Test Monitoring Service

Risk to Small Business: 1.667 = Severe
A number of Australian universities have been affected by a breach at testing services provider ProctorU. Hackers from the Shiny Hunters group published the stolen database from ProctorU online. The affected universities include the Group of Eight’s University of Sydney, University of NSW, University of Queensland, University of Melbourne, University of Western Australia, and the University of Adelaide, as well as Swinburne University, James Cook University, and Curtin University. The stolen data reportedly contains The data contains usernames, unencrypted passwords, legal names, and full residential addresses of students at the impacted schools.

Individual Risk: 2.871 = Moderate
No financial information was stolen, but student PII was impacted. Students should be cautious of spear phishing attempts using the stolen data
Customers Impacted: 444,267
How it Could Affect Your Customers’ Business: Ransomware has become the bane of most cybersecurity planners’ existence. By increasing investment in essential security awareness training tools, companies can better protect their data ( and their budgets) from ransomware.
ID Agent to the Rescue: Learn expert secrets and get growth-focused sales advice from a Channel All-Star in this powerful webinar that shows you how to land and close more security business in 5 proven practical steps to success. Download the webinar >>
The Week in Breach Cybersecurity and New Breach News Risk Levels
1 – 1.5 = Extreme Risk
1.51 – 2.49 = Severe Risk
2.5 – 3 = Moderate Risk
Risk scores for The Week in Breach Cybersecurity and New Breach News are calculated using a formula that considers a wide range of factors related to the assessed breach.
The Week in Breach Cybersecurity and New Breach News: Added Intelligence
Go Inside the Ink to Get the Inside Scoop on Cybersecurity and New Breach News
Every weekday, our blog features timely cybersecurity and breach news, problem-solving advice, and expert analysis of today’s threats, plus insight that helps you plan for tomorrow. Don’t miss it!
Catch up on what you need to know now:
- TwitterWas Compromised by a Phished Password – Can That Happen to You Too?
- 3 Tools to Stop Social Engineering Attacks in Their Tracks
- Level Up Your Business With These 3 MSP Webinars
- Want to Solve Data Breach Mysteries With Experts
- The Ink This Week: Cybersecurity News & Analysis 07/31/20
- 3 Lessons Learned from the Biggest Ransomware Attacks of 2020
Free eBook of the Week
In Cybersecurity and New Breach News This Week, Booming Dark Web Data Markets are Driving Crime
The pandemic has brought change to every corner of the world – including the Dark Web. Have you taken the time to learn what you need to know about today’s Dark Web to protect your customers and your MSP?
In order to guard systems and data against Dark Web dangers, you need to understand the way that business is done there – especially in the booming data markets of all kinds. Understanding the Dark Web economy will also help you better protect your customers (and yourself) against insider threats like malicious employees selling access, proprietary information, and specialty services in the hot “as a service” sector.
Learn about the changes that COVID-19 and a challenging global economy have brought to the Dark Web in our eBook “State of the Dark Web“. Then take an even deeper dive into Dark Web markets.
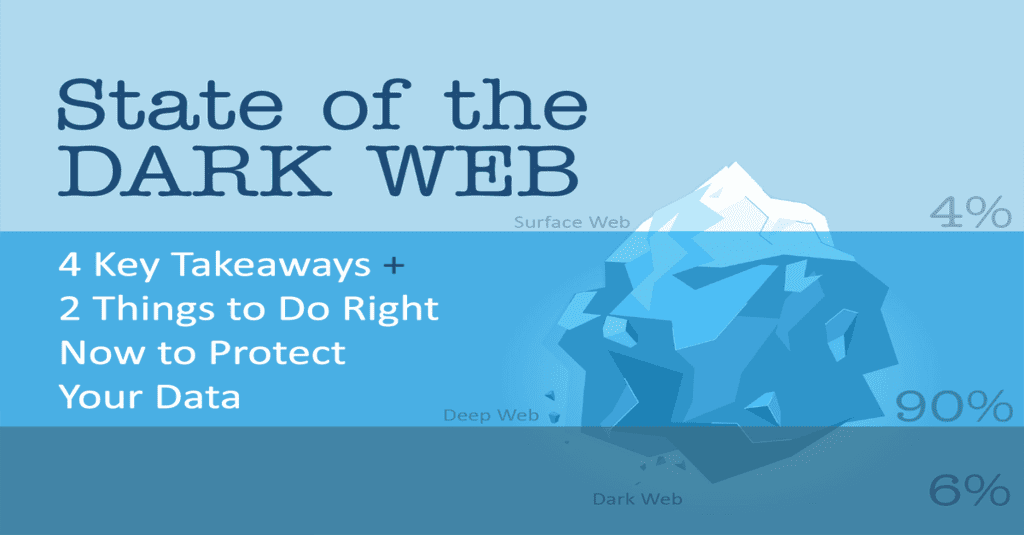
Download “State of the Dark Web” now. READ THE EBOOK NOW>>
New Breach News Spotlight
Nation State Actors Threaten Companies Worldwide
Cybersecurity threats and attacks involving nation state actors have been all over the news. From a pattern of suspected state-sponsored cyberattacks in Australia to suspected cyberthreats targeting critical infrastructure in the United States, high-level hacking has become a worldwide concern.
While this may not seem like a problem that could affect MSPs and small to medium-sized businesses, it is. These hackers aren’t just going for the biggest kid on the block. Smarter, more sophisticated hackers are starting from the ground up in a concerted effort to capture credentials and access to providers of essential business services in their webs.
KNOW YOUR HACKERS
By far, the most dangerous cybercrime environment right now is in medical research and development, as companies around the globe race to develop treatments and an eventual vaccine for COVID-19. Recent attempts to steal vaccine research from Moderna can be traced to known Chinese hacking groups. Additional attacks against pharmaceutical companies and researchers can be traced to Russian hacking groups, according to the U.S. National Security Agency.
Your customers are reading about these attacks in major publications and seeing growing concern from governments around the world in the media. That’s why you should develop a plan now to offer them options to increase their data protection – and using that plan to start conversations about increased security with other clients who you think might be at risk. Here are 2 crucial tools that should be on that plan.
SECURE GATEWAYS TO DATA
Immediately recommend that every customer add a secure identity and access management solution like Passly. The bane of every IT team, insecure or stolen passwords are a constant menace. Multifactor Authentication provides a crucial extra security check between bad actors and a company’s data and systems, and Single sign-on lets administrators quickly and efficiently turn on and off access to applications. Secure Central Password Storage Vaults also keep administrator credentials protected yet accessible by the right people when needed. Improving password security is vital to guarding against cyberattacks like these.
STOP RANSOMWARE ATTACKS FROM LANDING
Encourage customers to boost their phishing resistance training immediately. One of the most devastating tools that cybercriminals including nation state actors are using these days is ransomware – and the number one way that ransomware is delivered is through a phishing email. About 50% of businesses were affected by ransomware last year – but 50% of IT professionals don’t believe that their organization is ready to defend against a ransomware attack.
INFORMATION IS POWER
Giving your customers these essential protection tools can help guard against many of the major attack vectors that nation state hackers like to use, like credential stuffing and ransomware. Continuing to monitor for compromised credentials using Dark Web ID helps provide a clear picture of your clients’ potential threats as well (if you’re not already doing that, now is a great time to start).
Staying updated on new technologies and cost-effective solutions, gathering good intelligence, and staying informed about new threats is your best bet for providing effective protection to your clients and your MSP in a tumultuous world.
Get Ready To Maximize on Opportunities Created By New Breach News & Energize Your Business With These 3 New Webinars
Learn how to take advantage of the sales and marketing tools that Partners get from Powered Services to take your business to the next level!
Secure identity and access management using Passly is the key to guarding your customers’ systems and data (and your MSP)
Empower your clients to reduce their largest attack surface – their staff. See how improved security awareness and phishing resistance training including BullPhish ID will boost your clients’ defenses and your bottom line fast!
COMING SOON! CONNECT IT GLOBAL IS JUST AROUND THE CORNER ON AUGUST 24 – 27, 2020
Reserve your virtual space now for CONNECT IT GLOBAL! We’ve got an incredible lineup of education, certification, and networking opportunities plus lots of fun, prizes, contests, and so much more on the agenda – and expect some wonderful surprises!
Check out these highlights of what to expect:
- Earn new certifications: Certified Dark Web ID & BullPhish ID Administrator & Certified Passly Administrator
- See THE ID AGENT 2020 ROADMAP (must-see panel!)
- Attend THE NEW CONNECT 360 – THE MSP PROFITABILITY MINI-SYMPOSIUM
- Explore today’s biggest threat in GO PHISHING: DETECTING ADVANCED, PERSISTENT PHISHING THREATS
- Go inside a breach to think like a hacker in THE ANATOMY OF AN O365 BREACH
- Plus prizes, giveaways, networking opportunities & more!
Don’t miss this opportunity to earn new certifications, find out about new products and strategies, grow your knowledge, and connect with Channel All-Stars!
Catch Up With Us at These Virtual Events
AUG 24 – 27: Connect IT 2020 REGISTER >
AUG 30 – SEPT 1: Build IT 2020 REGISTER>>
SEPT 27 – 29: GlueX 2020 REGISTER>>
OCT 28 – 29: MSP CONNECT LIVE MIDWEST REGISTER>>
OCT 28 – 29: MSP CONNECT LIVE MIDWEST REGISTER>>
NOV 18 -19: MSP CONNECT LIVE MID-ATLANTIC REGISTER>>
DEC 2 – 4: MSP CONNECT SOUTHWEST REGISTER>>
A note about cybersecurity and new breach news for your customers:
FBI Warns Against Increased Danger From Netwalker Ransomware
Ransomware attacks are the monster in the closet that keeps IT teams up at night – and they’re only getting worse. Recently, the US Federal Bureau of Investigation released a new Flash Alert warning about the danger of Netwalker ransomware to businesses and infrastructure, as attacks with this tool ramp up against US-based targets.
Companies of all sizes are at risk for ransomware attacks of this nature, especially in the healthcare, infrastructure, defense, or technology sectors. Netwalker ransomware has also been used to disrupt production lines, as unfortunately happened to a manufacturer of respirators urgently needed in the fight against COVID-19.
To add to your defenses quickly, upgrade the protection on the access points to your data and systems by adding a secure identity and access management solution. Passly is an affordable and effective tool that combines multifactor authentication and single sign-on to create a more secure gateway to the heart of your business.
Adding a dynamic tool like Passly strengthens your defense against cybercrime like ransomware and password hacking fast. Passly deploys in days, not weeks – because in today’s fast-evolving threat atmosphere, no business has time to wait and see what cybercriminals are up to next.
Get high-quality marketing tools to help you connect with your customers with our free resources for marketing and education like eBooks, webinars, social media graphics, infographics, and more!.
Follow us on social media to find out about breach news, upcoming events, new blog posts, eBooks, white papers, webinars, product updates, marketing tools, and other cybersecurity news!
Are you an ID Agent Partner? Feel free to re-use this blog post (in part or in its entirety) for your own social media and marketing efforts. Just send an email to [email protected] to let us know – we welcome your feedback and we love to hear about how our content works for you!
Ready to become an ID Agent Partner or learn more about our remote-ready suite of cybersecurity solutions including the award-winning DarkWeb ID? Contact us today!